2017
- Yu, Yijun; Yang, Mu and Nuseibeh, Bashar (2017). Live Blackboxes: Requirements for Tracking and Verifying Aircraft in Motion. In: SCiA 2017 : 4th Software Challenges in Aerospace Symposium, 9–13 January 2017, Grapevine, Texas.
- Akiki, Pierre A.; Bandara, Arosha K. and Yu, Yijun (2017). Visual Simple Transformations: Empowering End-Users to Wire Internet of Things Objects. Transactions on Computer-Human Interaction (In Press).
- Lotz, Nicole and Sharp, Helen (2017). The influence of cognitive style, design setting and cultural background on sketch-based ideation by novice interaction designers. The Design Journal (In Press).
2016
- Akiki, Pierre A.; Bandara, Arosha K. and Yu, Yijun (2016). Engineering Adaptive Model-Driven User Interfaces. IEEE Transactions on Software Engineering, 42(12) pp. 1118–1147.
- Viana, Thiago; Bandara, Arosha and Zisman, Andrea (2016). Towards a Framework for Managing Inconsistencies in Systems of Systems. In: Colloquium on Software-intensive Systems-of-Systems at 10th European Conference on Software Architecture, 29th November 2016, Copenhagen.
- Paci, Patrizia; Mancini, Clara and Price, Blaine A. (2016). Designing for Wearability in Animal Biotelemetry. In: ACI'16, 16-17 Nov 2016, Milton Keynes, ACM.
- Perera, Charith; Mccormick, Ciaran; Bandara, Arosha; Price, Blaine and Nuseibeh, Bashar (2016). Privacy-by-Design Framework for Assessing Internet of Things Applications and Platforms. In: International Conference on the Internet of Things (IOT 2016), 7-9 November 2016, Stuttgart, Germany.
- Gray, Joshua; Franqueira, Virginia N. L. and Yu, Yijun (2016). Forensically-Sound Analysis of Security Risks of using Local Password Managers. In: 1st International Workshop on Requirements Engineering for Investigating and Countering Crime, 13 September 2016, Beijing, IEEE.
- Mehta, Vikram; Price, Blaine; Bandara, Arosha and Nuseibeh, Bashar (2016). Wearables for Physical Privacy. In: UbiComp 2016, 12-16 Sep 2016, Heidelberg, Germany.
- Tun, Thein; Price, Blaine; Bandara, Arosha; Yu, Yijun and Nuseibeh, Bashar (2016). Verifiable Limited Disclosure: Reporting and Handling Digital Evidence in Police Investigations. In: iRENIC: 1st International Workshop on Requirements Engineering for Investigating and Countering Crime, 12th September 2016, Beijing, China.
- Peng, Xin; Gu, Jingxiao; Tan, Tian Huat; Sun, Jun; Yu, Yijun; Nuseibeh, Bashar and Zhao, Wenyun (2016). CrowdService: Serving the Individuals through Mobile Crowdsourcing and Service Composition. In: Proceedings of the31st ACM/IEEE international conference on Automated software engineering, ACM, New York, USA, (In press).
- Bennaceur, Amel and Nuseibeh, Bashar (2016). The Many Facets of Mediation: A Requirements-driven Approach for Trading-off Mediation Solutions. In: Mistrík, Ivan; Ali, Nour; Grundy, John; Kazman, Rick and Schmerl, Bradley eds. Managing trade-offs in adaptable software architectures. Elsevier.
- Gregory, Peggy; Barroca, Leonor; Sharp, Helen; Deshpande, Advait and Taylor, Katie (2016). The challenges that challenge: Engaging with agile practitioners’ concerns. Information and Software Technology, 77 pp. 92–104.
- Sharp, Helen; Dittrich, Yvonne and de Souza, Cleidson (2016). The Role of Ethnographic Studies in Empirical Software Engineering. IEEE Transactions on Software Engineering, 42(8) pp. 786–804.
- Katz, Dmitri; Dalton, Nick; Holland, Simon; O'Kane, Aisling and Price, Blaine A. (2016). Questioning the Reflection Paradigm for Diabetes Mobile Apps. In: EAI International Conference on Wearables in Healthcare, 14-15 June 2016, Budapest, European Alliance for Innovation.
- Pasquale, Liliana; Hanvey, Sorren; Mcgloin, Mark and Nuseibeh, Bashar (2016). Adaptive evidence collection in the cloud using attack scenarios. Computers & Security, 59 pp. 236–254.
- Calikli, Gul; Law, Mark; Bandara, Arosha K.; Russo, Alesandra; Dickens, Luke; Price, Blaine A.; Stuart, Avelie; Levine, Mark and Nuseibeh, Bashar (2016). Privacy Dynamics: Learning Privacy Norms for Social Software. In: 2016 IEEE/ACM 11th International Symposium on Software Engineering for Adaptive and Self-Managing Systems, Association of Computing Machinery pp. 47–56.
- Dilshener, Tezcan; Wermelinger, Michel and Yu, Yijun (2016). Locating Bugs without Looking Back. In: MSR '16: Proceedings of the 13th International Conference on Mining Software Repositories, ACM, New York, pp. 286–290.
- García-Galán , Jesús ; Pasquale , Liliana ; Grispos , George and Nuseibeh, Bashar (2016). Towards Adaptive Compliance. In: SEAMS '16: Proceedings of the 11th International Workshop on Software Engineering for Adaptive and Self-Managing Systems, ACM, New York, pp. 108–114.
- Tsigkanos, Christos; Kehrer, Timo; Ghezzi, Carlo; Pasquale, Liliana and Nuseibeh, Bashar (2016). Adding static and dynamic semantics to building information models. In: SEsCPS '16: Proceedings of the 2nd International Workshop on Software Engineering for Smart Cyber-Physical Systems, ACM, New York, USA, pp. 1–7.
- Mehta, Vikram; Bandara, Arosha; Price, Blaine and Nuseibeh, Bashar (2016). Privacy Itch and Scratch: On Body Privacy Warnings and Controls. In: ACM Conference on Human Factors in Computing Systems, ACM, San Jose, 34.
- Leigh, Andrew; Wermelinger, Michel and Zisman, Andrea (2016). An Evaluation of Design Rule Spaces as Risk Containers. In: Proceedings of the Working International Conference on Software Architecture, 5-8 April 2016, IEEE.
- Barhamgi, Mahmoud; Bandara, Arosha K.; Yu, Yijun; Belhajjame, Khalid and Nuseibeh, Bashar (2016). Protecting Privacy in the Cloud: Current Practices, Future Directions. Computer, 49(2) pp. 68–72.
- Barroca, Leonor; Sharp, Helen; Salah, Dina; Taylor, Katie and Gregory, Peggy (2016). Bridging the gap between research and agile practice: an evolutionary model. International Journal of System Assurance Engineering and Management (Early view).
- Bennaceur, Amel; Mccormick, Ciaran; García Galán, Jesús; Naranwala Gonaduwage, Charith; Smith, Andrew; Zisman, Andrea and Nuseibeh, Bashar (2016). Feed me, Feed me: An Exemplar for Engineering Adaptive Software. In: 11th International Symposium on Software Engineering for Adaptive and Self-Managing Systems, 16-17 May 2016.
- Deshpande, Advait; Sharp, Helen; Barroca, Leonor and Gregory, Peggy (2016). Remote Working and Collaboration in Agile Teams. In: International Conference on Information Systems, 11-14 December 2016, Dublin (forthcoming).
- Paci, Patrizia; Mancini, Clara and Price, Blaine A. (2016). Towards a Wearer-Centred Framework for Animal Biotelemetry. In: Proceedings of Measuring Behaviour 2016 (Spink, A.J ed.), 25-27 May 2016, Dublin.
- Perera, Charith; Wakenshaw, Susan Y. L.; Baarslag, Tim; Haddadi, Hamed; Bandara, Arosha K.; Mortier, Richard; Crabtree, Andy; Ng, Irene C. L.; McAuley, Derek and Crowcroft, Jon (2016). Valorising the IoT Databox: creating value for everyone. Transactions on Emerging Telecommunications Technologies (Early access).
- Tsigkanos, Christos; Pasquale, Liliana; Ghezzi, Carlo and Nuseibeh, Bashar (2016). On the Interplay Between Cyber and Physical Spaces for Adaptive Security. IEEE Transactions on Dependable and Secure Computing (early access).
2015
- Cavero, Jose; Wermelinger, Michel and Wolff, Annika (2015). Some future scenarios for ‘in the wild’ visualisations. In: Death of the Desktop: Envisioning Visualization without Desktop Computing Workshop, 09 November 2014, Paris.
- Yu, Yijun (2015). The aftermath of mystery flight MH370: what can engineers do? Proceedings of the IEEE, 103(11) pp. 1948–1951.
- Zhang, Tian; Pan, Minxue; Zhao, Jizhou; Yu, Yijun and Li, Xuandong (2015). An open framework for semantic code queries on heterogeneous repositories. In: Proceedings of the 2015 International Symposium on Theoretical Aspects of Software Engineering (Sun, Jun ed.), IEEE, pp. 39–46.
- Butler, Simon; Wermelinger, Michel and Yu, Yijun (2015). Investigating naming convention adherence in Java references. In: Proceedings of 2015 IEEE 31st International Conference on Software Maintenance and Evolution (ICSME), IEEE, pp. 41–50.
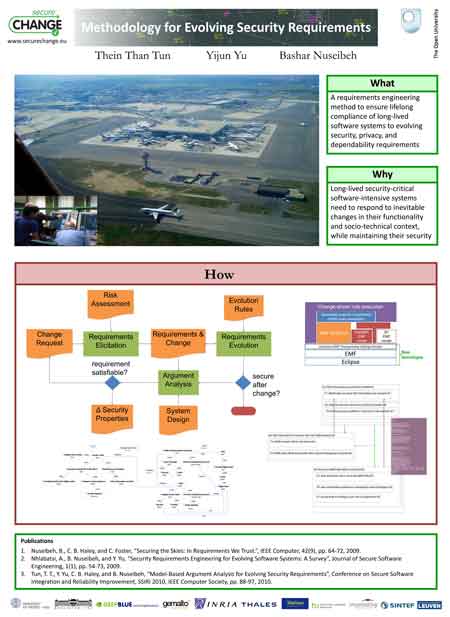
- Yu, Yijun; Franqueira, Virginia N. L.; Tun, Thein; Wieringa, Roel J. and Nuseibeh, Bashar (2015). Automated analysis of security requirements through risk-based argumentation. Journal of Systems and Software, 106 pp. 102–116.
- Nhlabatsi, Armstrong; Yu, Yijun; Zisman, Andrea; Tun, Thein; Khan, Niamul; Bandara, Arosha; Khan, Khaled and Nuseibeh, Bashar (2015). Managing security control assumptions using causal traceability. In: 8th International Symposium on Software and Systems Traceability (SST 2015), 17 July 2015, Florence, Italy.
- Bourgeois, Jacky; Kortuem, Gerd; Baudry, Benoit; van der Linden, Janet; Bourcier, Johann and Price, Blaine A. (2015). Understanding and Supporting Emerging Domestic Energy Practices. In: British HCI Conference - 'Sustainable HCI in the UK' workshop, 13 - 17 July 2015, Lincoln.
- Stiver, Alexandra; Barroca, Leonor; Petre, Marian; Richards, Michael and Roberts, Dave (2015). Civic crowdfunding: how do offline communities engage online? In: Proceedings of the 2015 British HCI Conference, ACM, pp. 37–45.
- Bennaceur, Amel; Andriescu , Emil; Speicys Cardoso, Roberto and Issarny, Valérie (2015). A unifying perspective on protocol mediation: interoperability in the Future Internet. Journal of Internet Services and Applications, 6(12)
- Segal, Judith; Petre, Marian and Sharp, Helen (2015). The future of e-infrastructures. Computing in Science & Engineering, 17(3) pp. 78–84.
- Butler, Simon; Wermelinger, Michel and Yu, Yijun (2015). A survey of the forms of Java reference names. In: Proceedings of the 2015 IEEE 23rd International Conference on Program Comprehension, IEEE Press, pp. 196–206.
- Gregory, Peggy; Barroca, Leonor; Taylor, Katie; Salah, Dina and Sharp, Helen (2015). Agile challenges in practice: a thematic analysis. In: 16th International Conference on Agile Software Development, XP 2015, 25-29 May 2015, Helsinki.
- Tun, Thein; Lutz, Robyn; Nakayama, Brian; Yu, Yijun; Mathur, Divita and Nuseibeh, Bashar (2015). The Role of Environmental Assumptions in Failures of DNA Nanosystems. In: 2015 IEEE/ACM 1st International Workshop on Complex Faults and Failures in Large Software Systems (COUFLESS), pp. 27–33.
- Wermelinger, Michel; Hall, Jon; Rapanotti, Lucia; Barroca, Leonor; Ramage, Magnus and Bandara, Arosha (2015). Teaching software systems thinking at The Open University. In: Proceedings of the 37th International Conference on Software Engineering, IEEE, pp. 307–310.
- Wermelinger, Michel and Yu, Yijun (2015). An architectural evolution dataset. In: Proceedings of the 12th Working Conference on Mining Software Repositories, IEEE, pp. 502–505.
- Bennaceur, Amel and Issarny, Valérie (2015). Automated synthesis of mediators to support component interoperability. IEEE Transactions on Software Engineering, 41(3) pp. 221–240.
- Akiki, Pierre A.; Bandara, Arosha K. and Yu, Yijun (2015). Adaptive model-driven user interface development systems. ACM Computing Surveys, 47(1), article no. 9.
- Katz, Dmitri; Dalton, Nicholas and Price, Blaine (2015). Failing the challenge: Diabetes apps & long-term daily adoption. In: 8th International Conference on Advanced Technologies & Treatments for Diabetes (ATTD 2015), 18-21 Feb 2015, Paris.
- Preece, Jenny; Rogers, Yvonne and Sharp, Helen (2015). Interaction Design: Beyond human-computer interaction (4th ed). Chichester: John Wiley & Sons.
- Mangano, N.; LaToza, T.; Petre, M. and van der Hoek, A. (2015). How software designers interact with sketches at the whiteboard. IEEE Transactions on Software Engineering, 41(2) pp. 135–156.
- Pawlik, Aleksandra; Segal, Judith; Petre, Marian and Sharp, Helen (2015). Crowdsourcing scientific software documentation: a case study of the NumPy documentation project. Computing in Science & Engineering , 17(1) pp. 28–36.
- Nhlabatsi, Armstrong; Tun, Thein; Khan, Niamul; Yu, Yijun; Bandara, Arosha; Khan, Khaled M. and Nuseibeh, Bashar (2015). “Why can’t I do that?”: tracing adaptive security decisions. EAI Endorsed Transactions on Self-Adaptive Systems, 1(1), article no. e2.
- Plonka, Laura; Sharp, Helen; van der Linden, Janet and Dittrich, Yvonne (2015). Knowledge transfer in pair programming: an in-depth analysis. International Journal of Human-Computer Studies, 73(1) pp. 66–78.
- Rawassizadeh, Reza; Price, Blaine A. and Petre, Marian (2015). Wearables: has the age of smartwatches finally arrived? Communications of the ACM, 58(1) pp. 45–47.
- Bjarnason, Elizabeth and Sharp, Helen (2015). The role of distances in requirements communication: a case study. Requirements Engineering (Early view).
- Elbanhawy, Eiman and Price, Blaine A. (2015). Understanding the social practice of EV workplace charging. In: Adjunct Proceedings UbiComp/ISWC'15, ACM, pp. 1133–1141.
2014
- Yu, Yijun; Piwek, Paul; Tun, Thein Than and Nuseibeh, Bashar (2014). Towards explaining rebuttals in security arguments. In: 14th Workshop on Computational Models of Natural Argument, 10 December 2014, Krakow, Poland.
- Petre, Marian; Minocha, Shailey and Barroca, Leonor (2014). Digital technologies for doctoral dialogues at a distance. In: 2014 IEEE Frontiers in Education: Opening doors to Innovation and Internationalization in Engineering Education Conference, 22-25 October 2014, Madrid, Spain, pp. 2432–2439.
- Petre, Marian (2014). ‘No shit’ or ‘Oh, shit!’: responses to observations on the use of UML in professional practice. Software and Systems Modeling, 13(4) pp. 1225–1235.
- Yang, Mu; Yu, Yijun; Bandara, Arosha and Nuseibeh, Bashar (2014). Adaptive sharing for online social networks: a trade-off between privacy risk and social benefit. In: 13th IEEE International Conference on Trust, Security and Privacy in Computing and Communications (IEEE TrustCom-14), 24-26 September 2014, Beijing, China, IEEE, pp. 45–52.
- Calikli, Gul; Andersen, Mads Schaarup; Bandara, Arosha; Price, Blaine A. and Nuseibeh, Bashar (2014). Personal Informatics for Non-Geeks: Lessons Learned from Ordinary People. In: Proceedings of 2014 ACM International Joint Conference on Pervasive and Ubiquitous Computing Adjunct Publication (UbiComp 2014 Adjunct), pp. 683–686.
- Petre, Marian and Wilson, Greg (2014). Code review for and by scientists: preliminary findings. In: 2nd Workshop on Sustainable Software for Science: Practice and Experiences (WSSSPE2), 16 November 2014, New Orleans, LA, USA.
- Bourgeois, Jacky; Kortuem, Gerd; Bourcier, Johann; van der Linden, Janet; Price, Blaine A. and Baudry, Benoit (2014). Energy Demand Shifting in Residential Households: The Interdependence between Social Practices and Technology Design. In: Behave 2014, 3-4 Oct 2014, Oxford.
- Bourgeois, Jacky; van der Linden, Janet; Kortuem, Gerd; Price, Blaine A. and Rimmer, Christopher (2014). Conversations with my washing machine: an in-the-wild study of demand-shifting with self-generated energy. In: 2014 ACM International Joint Conference on Pervasive and Ubiquitous Computing (UbiComp 2014), 13-17 September 2014, Seattle, Washington, US, ACM, pp. 459–470.
- Kortuem, Gerd; Bourgeois, Jacky; van der Linden, Janet and Price, Blaine (2014). Participatory Data Analysis: A New Method for Investigating Human Energy Practices. In: CEUR Workshop Proceedings (Penzenstadler, Birgit and Lohmann , Wolfgang eds.), 1203 pp. 35–37.
- Bennaceur, Amel and Issarny, Valérie (2014). Layered connectors: revisiting the formal basis of architectural connection for complex distributed systems. In: ECSA'14 - The 8th European Conference on Software Architecture.
- Bourgeois, J.; van der Linden, J.; Kortuem, G.; Price, B. A. and Rimmer, C. (2014). Using participatory data analysis to understand social constraints and opportunities of electricity demand-shifting. In: 2nd International Conference on ICT for Sustainability (ICT4S 2014), 24-27 August 2014, Stockholm, Sweden, Atlantis Press.
- Nhlabatsi, Armstrong; Tun, Thein; Khan, Niamul; Yu, Yijun; Bandara, Arosha; Khan, Khaled and Nuseibeh, Bashar (2014). Traceability for adaptive information security in the cloud. In: Proceedings of the 2014 IEEE Seventh International Conference on Cloud Computing, IEEE, pp. 958–959.
- Bailey, Christopher; Montrieux, Lionel; de Lemos, Rogério; Yu, Yijun and Wermelinger, Michel (2014). Run-time generation, transformation, and verification of access control models for self-protection. In: SEAMS 2014 Proceedings of the 9th International Symposium on Software Engineering for Adaptive and Self-Managing Systems, ACM, pp. 135–144.
- Chen, Bihuan; Peng, Xin; Yu, Yijun; Nuseibeh, Bashar and Zhao, Wenyun (2014). Self-adaptation through incremental generative model transformations at runtime. In: 36th International Conference on Software Engineering, Hyderabad, ACM/IEEE.
- Lotz, Nicole; Sharp, Helen; Woodroffe, Mark; Blyth, Richard; Rajah, Dino and Ranganai, Turugare (2014). Framing behaviours in novice interaction designers. In: Proceedings of DRS 2014: Design's Big Debates, Umeå Institute of Design, Umeå University, pp. 1178–1190.
- Thomas, Keerthi; Bandara, Arosha K.; Price, Blaine A. and Nuseibeh, Bashar (2014). Distilling Privacy Requirements for Mobile Applications. In: 36th International Conference on Software Engineering (ICSE 2014), 31 May-7 June, 2014, Hyderabad, India.
- Plonka, Laura; Sharp, Helen; Gregory, Peggy and Taylor, Katie (2014). UX design in agile: a DSDM case study. In: Agile Processes in Software Engineering and Extreme Programming: 15th International Conference, XP 2014, Lecture Notes in Business Information Processing, Springer.
- Chen, Bihuan; Peng, Xin; Yu, Yijun and Zhao, Wenyun (2014). Uncertainty handling in goal-driven self-optimization – limiting the negative effect on adaptation. Journal of Systems and Software, 90 pp. 114–127.
- Akiki, Pierre A.; Bandara, Arosha K. and Yu, Yijun (2014). Integrating adaptive user interface capabilities in enterprise applications. In: 36th International Conference on Software Engineering (ICSE 2014), 31 May-7 June, 2014, Hyderabad, India, ACM.
- Bennaceur, Amel; Bandara, Arosha; Jackson, Michael; Liu, Wei; Montrieux, Lionel; Tun, Thein; Yu, Yijun and Nuseibeh, Bashar (2014). Requirements-driven mediation for collaborative security. In: SEAMS'14 - The 9th International Symposium on Software Engineering for Adaptive and Self-Managing Systems, 2-3 June 2014, Hyderabad.
- Bennaceur, Amel; France, Robert B.; Tamburrelli, Giordano; Vogel, Thomas; Mosterman, Pieter J.; Cazzola, Walter; Costa, Fábio M.; Pierantonio, Alfonso; Tichy, Matthias; Akşit, Mehmet; Emmanuelson, Pär; Gang, Huang; Georgantas, Nikolaos and Redlich, David (2014). Mechanisms for leveraging models at runtime in self-adaptive software. In: Bencomo, Nelly; France, Robert B.; Cheng, Betty H. and Assmann, Uwe eds. Models@run.time: Foundations, Applications, and Roadmaps. Lecture Notes in Computer Science (8378). Cham: Springer , 19-46 .
- Chen, Bihuan; Peng, Xin; Yu, Yijun and Zhao, Wenyun (2014). Requirements-driven self-optimization of composite services using feedback control. IEEE Transactions on Services Computing, 8(1) pp. 107–120.
- Felderer, Michael; Katt, Basel; Kalb, Philipp; Jürjens, Jan; Ochoa, Martín; Paci, Federica; Tran, Le Minh Sang; Tun, Thein; Yskout, Koen; Scandariato, Riccardo; Piessens, Frank; Vanoverberghe, Dries; Fourneret, Elizabeta; Gander, Matthias; Solhaug, Bjørnar and Breu, Ruth (2014). Evolution of security engineering artifacts: a state of the art survey. International Journal of Secure Software Engineering, 5(4) pp. 48–98.
- Mangano, Nicolas; LaToza, Thomas D.; Petre, Marian and van der Hoek, André (2014). Supporting informal design with interactive whiteboards. In: CHI '14 Proceedings of the SIGCHI Conference on Human Factors in Computing Systems, ACM, pp. 331–340.
- Pasquale, Liliana; Ghezzi, Carlo; Menghi, Claudio; Tsigkanos, Christos and Nuseibeh, Bashar (2014). Topology aware adaptive security. In: Proceedings of the 9th International Symposium on Software Engineering for Adaptive and Self-Managing Systems, ACM, pp. 43–48.
- Petre, Marian and Damian, Daniela (2014). Methodology and culture: drivers of mediocrity in software engineering? In: FSE 2014 Proceedings of the 22nd ACM SIGSOFT International Symposium on Foundations of Software Engineering, ACM, pp. 829–832.
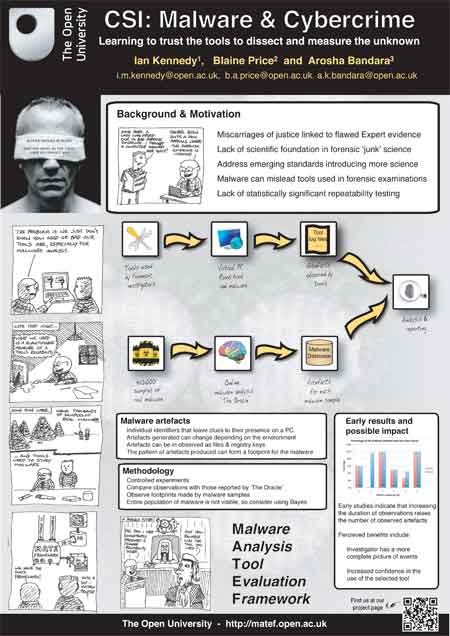
- Price, B.A.; Janicke, H.; Lallie, H.S.; Sinclair, J.E.; Joy, M.S. and Howley, R. (2014). Pedagogic Challenges in Teaching Cyber Security – a UK perspective. In: ICC 2014 - Computer Networks and Security (Venugopal, K.R. and Lingareddy, S.C. eds.), Elsevier, pp. 605–615.
- Tsigkanos, Christos; Pasquale, Liliana; Menghi, Claudio; Ghezzi, Carlo and Nuseibeh, Bashar (2014). Engineering topology aware adaptive security: preventing requirements violations at runtime. In: 2014 IEEE 22nd International Requirements Engineering Conference (RE): Proceedings, Institute of Electrical and Electronics Engineers, pp. 203–212.
- Yu, Yijun; Tun, Thein Than; Bandara, Arosha K.; Zhang, Tian and Nuseibeh, Bashar (2014). From model-driven software development processes to problem diagnoses at runtime. In: Bencome, Nelly; France, Robert; Cheng, Betty H.C. and Aßmann, Uwe eds. Models@run.time -- Foundations, Applications, and Roadmaps. Lecture Notes in Computer Science (8378). Cham: Springer International Publishing, pp. 188–207.
2013
- Silva, Icamaan and Zisman, Andrea (2013). Decomposing ratings in service compositions. In: 11th International Conference on Service Oriented Computing, 2-5 December, 2013, Berlin, Springer.
- Abelein, Ulrike; Sharp, Helen and Paech, Barbara (2013). Does involving users in software development really influence system success? IEEE Software, 30(6) pp. 17–23.
- Tun, Thein; Yu, Yijun; Jackson, Michael; Laney, Robin and Nuseibeh, Bashar (2013). Aspect interactions: a requirements engineering perspective. In: Moreira, Ana; Chitchyan, Ruzanna; Araujo, João and Rashid, Awais eds. Aspect-Oriented Requirements Engineering. Heidelberg: Springer, pp. 271–286.
- Yu, Yijun; Peng, Xin and Leite, Julio Cesar Sampaio do Prado (2013). Reasoning about dynamic aspectual requirements. In: Moreira, Ana; Chitchyan, Ruzanna; Araújo, João and Rashid, Awais eds. Aspect-Oriented Requirements Engineering. Heidelberg: Springer, pp. 23–42.
- Van Der Hoek, Andre and Petre, Marian (2013). Software Designers in Action: A Human-Centric Look at Design Work. Chapman & Hall/CRC Innovations in Software Engineering and Software Development Series. Abingdon: Chapman and Hall/CRC.
- Sharp, Helen; Lotz, Nicole; Blyth, Richard; Woodroffe, Mark; Rajah, Dino and Ranganai, Turugare (2013). A protocol study of novice interaction design behaviour in Botswana: solution-driven interaction design. In: BCS HCI Conference 2013, 9-13 September 2013, London.
- Hubaux, Arnaud; Tun, Thein Than and Heymans, Patrick (2013). Separation of concerns in feature diagram languages: a systematic survey. ACM Computing Surveys, 45(4), article no. 51.
- Lohar, Sugandha; Amornborvornwong, Sorowit; Zisman, Andrea and Cleland-Huang, Jane (2013). Improving trace accuracy through data-driven configuration and composition of tracing features. In: 9th Joint Meeting of the European Software Engineering Conference and the ACM SIGSOFT Symposium on the Foundations of Software Engineering, 18-26 August 2013, St Petersburg, Russia, ACM, pp. 378–388.
- Lotz, Nicole; Sharp, Helen; Woodroffe, Mark; Richard, Blyth; Rajah, Dino and Ranganai, Turugare (2013). Co-evolving problems and solutions: The case of novice interaction designers in Botswana and the UK. In: IASDR, 26-30 August, Tokyo, Japan, International Association of Societies of Design Research, pp. 1004–1015.
- Pasquale, Liliana; Yu, Yijun; Salehie, Mazeiar; Cavallaro, Luca; Tun, Thein Than and Nuseibeh, Bashar (2013). Requirements-driven adaptive digital forensics. In: 21st IEEE Requirements Engineering Conference, 15-19 July, 2013, Rio de Janeiro, Brazil.
- Taubenberger, Stefan; Jurjens, Jan; Yu, Yijun and Nuseibeh, Bashar (2013). Resolving vulnerability identification errors using security requirements on business process models. Information Management and Computer Security, 21(3) pp. 202–223.
- Dong, Rui-Zhi; Peng, Xin; Yu, Yi-Jun and Zhao, Wen-Yun (2013). Requirements-driven self-repairing against environmental failures. In: 7th International Symposium on Theoretical Aspects of Software Engineering, 1-3 July 2013, Birmingham.
- Montrieux, Lionel; Yu, Yijun and Wermelinger, Michel (2013). Developing a domain-specific plug-in for a modelling platform: the good, the bad, the ugly. In: 3rd Workshop on Developing Tools as Plug-ins, 21 May 2013, San Francisco.
- Montrieux, Lionel; Yu, Yijun; Wermelinger, Michel and Hu, Zhenjiang (2013). Issues in representing domain-specific concerns in model-driven engineering. In: Workshop on Modeling in Software Engineering @ ICSE 2013, 18-19 May 2013, San Francisco.
- Petre, Marian (2013). UML in practice. In: 35th International Conference on Software Engineering (ICSE 2013), 18-26 May 2013, San Francisco, CA, USA, pp. 722–731.
- Bourgeois, Jacky; van der Linden, Janet; Price, Blaine and Kortuem, Gerd (2013). Technology probes: experiences with home energy feedback. In: Methods for Studying Technology in the Home, 27 Apr 2013, Paris.
- Omoronyia, Inah; Cavallaro, Luca; Salehie, Mazeiar; Pasquale, Liliana and Nuseibeh, Bashar (2013). Engineering adaptive privacy: on the role of privacy awareness requirements. In: 35th International Conference on Software Engineering (ICSE 2013), 18-26 May 2013, San Francisco, CA, USA (forthcoming), pp. 632–641.
- Hartnett, Elizabeth; Minocha, Shailey; Palmer, Jane; Petre, Marian; Evans, Shirley; Middup, Christopher Paul; Dunn, Kathryn; Murphy, Brendan; Heap, Tania and Roberts, Dave (2013). Older people and online social interactions: an empirical investigation. In: The UKAIS International Conference on Information Systems (UKAIS), 18-20 March 2013, Worcester College, University of Oxford.
- Bencomo, N.; Bennaceur, A.; Grace, P.; Blair, G. and Issarny, V. (2013). The role of models@run.time in supporting on-the-fly interoperability. Computing, 95(3) pp. 167–190.
- Price, Blaine; van der Linden, Janet; Bourgeois, Jacky and Kortuem, Gerd (2013). When looking out of the window is not enough: informing the design of in-home technologies for domestic energy microgeneration. In: First International Conference on Information and Communication Technologies for Sustainability, 14-16 February 2013, Zurich, Switzerland.
- Kortuem, Gerd; Bandara, Arosha; Smith, Neil; Richards, Michael and Petre, Marian (2013). Educating the Internet-of-Things generation. Computer, 46(2) pp. 53–61.
- Akiki, Pierre; Bandara, Arosha and Yu, Yijun (2013). Cedar Studio: an IDE supporting adaptive model-driven user interfaces for enterprise applications. In: Fifth ACM SIGCHI Symposium on Engineering Interactive Computing Systems (EICS 2013), 24–27 June 2013, London, UK.
- Akiki, Pierre; Bandara, Arosha and Yu, Yijun (2013). Crowdsourcing user interface adaptations for minimizing the bloat in enterprise applications. In: Fifth ACM SIGCHI Symposium on Engineering Interactive Computing Systems (EICS 2013), 24–27 June 2013, London, UK.
- Akiki, Pierre; Bandara, Arosha and Yu, Yijun (2013). Preserving designer input on concrete user interfaces using constraints while maintaining adaptive behavior. In: 2nd Workshop on Context-Aware Adaptation of Service Front-Ends (CASFE 2013), 24 June 2013, London, UK.
- Akiki, Pierre; Bandara, Arosha and Yu, Yijun (2013). RBUIS: simplifying enterprise application user interfaces through engineering role-based adaptive behavior. In: Fifth ACM SIGCHI Symposium on Engineering Interactive Computing Systems (EICS 2013), 24–27 June 2013, London, UK, ACM New York, NY, USA, pp. 3–12.
- Bennaceur, Amel; Chilton, Chris; Isberner, Malte and Jonsson, Bengt (2013). Automated mediator synthesis: combining behavioural and ontological reasoning. In: Software Engineering and Formal Methods, Springer-Verlag, pp. 274–288.
- Bennaceur, Amel; Issarny, Valérie; Johansson, Richard; Moschitti, Alessandro; Spalazzese, Romina and Sykes, Daniel (2013). Automatic service categorisation through machine learning in emergent middleware. In: Formal Methods for Components and Objects, Springer, pp. 133–149.
- Bennaceur, Amel; Issarny, Valérie; Sykes, Daniel; Howar, Falk; Isberner, Malte; Steffen, Bernhard; Johansson, Richard and Moschitti, Alessandro (2013). Machine learning for emergent middleware. In: Trustworthy Eternal Systems via Evolving Software, Data and Knowledge, Springer, pp. 16–29.
- Butler, Simon; Wermelinger, Michel; Yu, Yijun and Sharp, Helen (2013). INVocD: Identifier Name Vocabulary Dataset. In: 10th Working Conference on Mining Software Repositories, 18-19 May 2013, San Francisco.
- Hubaux, Arnaud; Acher, Mathieu; Tun, Thein Than; Heymans, Patrick; Collet, Philippe and Lahire, Philippe (2013). Separating concerns in feature models: retrospective and support for multi-views. In: Reinhartz-Berger, Iris; Sturm, Arnon; Clark, Tony; Cohen, Sholom and Bettin, Jorn eds. Domain Engineering: Product Lines, Languages, and Conceptual Models. Berlin: Springer, pp. 3–28.
- Issarny, Valérie and Bennaceur, Amel (2013). Composing distributed systems: overcoming the interoperability challenge. In: Elena, Giachino; Reiner, Hähnle; Frank, de Boer and Marcello, Bosangue eds. Formal Methods for Components and Objects. Lecture Notes in Computer Science (7866). Berlin: Springer, pp. 168–196.
- Moore, Kevin and Wermelinger, Michel (2013). The Challenge of Software Complexity. In: Proceedings of the European Conference on Complex Systems 2012, pp. 179–187.
- Peng, Xin; Xing, Zhenchang; Tan, Xi; Yu, Yijun and Zhao, Wenyun (2013). Improving feature location using structural similarity and iterative graph mapping. Journal of Systems and Software, 86(3) pp. 664–676.
- Saleem, Saad Bin; Montrieux, Lionel; Yu, Yijun; Tun, Thein and Nuseibeh, Bashar (2013). Maintaining security requirements of software systems using evolving crosscutting dependencies. In: Chitchyan, Ruzanna; Moreira, Ana; Araujo, Joao and Rashid, Awais eds. Aspect Oriented Requirements Engineering. Springer.
- Tun, Thein; Laney, Robin; Yu, Yijun and Nuseibeh, Bashar (2013). Specifying software features for composition: a tool-supported approach. Computer Networks, 57(12) pp. 2454–2464.
- Zisman, A.; Spanoudakis, G.; Dooley, J. and Siveroni, I. (2013). Proactive and reactive runtime service discovery: a framework and its evaluation. IEEE Transactions on Software Engineering, 39(7) pp. 954–974.
2012
- Hundhausen, C. D.; Fairbrother, D. and Petre, M. (2012). An empirical study of the “prototype walkthrough”: a studio-based activity for HCI education. ACM Transactions on Computer-Human Interaction (TOCHI), 19(4), article no. 26.
- Sajjad, Ali; Zisman, Andrea; Rajarajan, Muttukrishnan; Nair, Srijith K. and Dimitrakos, Theo (2012). Secure communication using dynamic VPN provisioning in an Inter-Cloud environment. In: Networks (ICON), 2012 18th IEEE International Conference On , IEEE, pp. 428–433.
- da Silva, Icamaan and Zisman, Andrea (2012). A framework for trustworthy services. In: Service-Oriented Computing : 10th International Conference, ICSOC 2012, Shanghai, China, November 12-15, 2012. Proceedings, Lecture Notes in Computer Science, Springer Berlin Heidelberg, pp. 328–343.
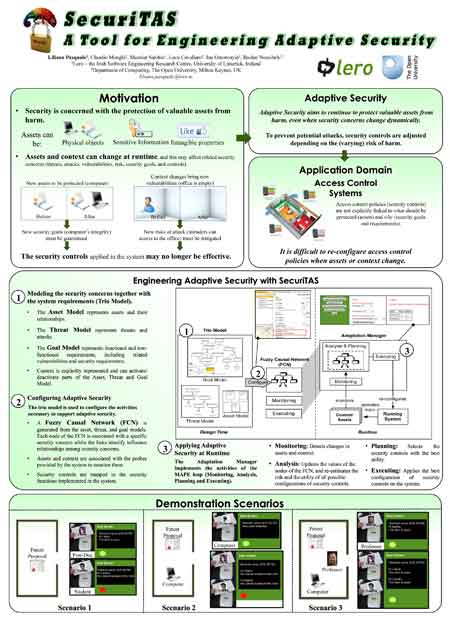
- Pasquale, Liliana; Menghi, Claudio; Salehie, Mazeiar; Cavallaro, Luca; Omoronyia, Inah and Nuseibeh, Bashar (2012). SecuriTAS: a tool for engineering adaptive security. In: ACM SIGSOFT 20th International Symposium on Foundations of Software Engineering (FSE 2012), 11-16 November 2012, North Carolina, USA.
- Fu, Lingxiao; Peng, Xin; Yu, Yijun; Mylopoulos, John and Zhao, Wenyun (2012). Stateful requirements monitoring for self-repairing socio-technical systems. In: 20th IEEE International Requirements Engineering Conference, 24-28 September 2012 , Chicago, Illinois.
- Blyth, Richard; Schadewitz, Nicole; Sharp, Helen; Woodroffe, Mark; Rajah, Dino and Turugare, Ranganai (2012). A frame signature matrix for analysing and comparing interaction design behaviour. In: BCS HCI Conference, 12-14 September 2012, Birmingham.
- Dyba, Tore and Sharp, Helen (2012). What's the evidence for Lean? IEEE Software, 29(5) pp. 19–21.
- Minocha, Shailey and Petre, Marian (2012). Handbook of Social Media for Researchers and Supervisors. The Open University.
- Ferreira, Jennifer; Sharp, Helen and Robinson, Hugh (2012). Agile development and user experience design integration as an ongoing achievement in practice. In: Agile 2012, 13-17 August 2012, Dallas, TX, pp. 11–20.
- Salifu, Mohammed; Yu, Yijun; Bandara, Arosha K. and Nuseibeh, Bashar (2012). Analysing monitoring and switching problems for adaptive systems. Journal of Systems and Software, 85(12) pp. 2829–2839.
- Bergin, Joseph; Eckstein, Jutta; Volter, Markus; Sipos, Marianna; Wallingford, Eugene; Marquardt, Klaus; Chandler, Jane; Sharp, Helen and Manns, Mary Lynn eds. (2012). Pedagogical Patterns: Advice For Educators. Joseph Bergin Software Tools.
- Yu, Yijun; Lin, Yu; Hu, Zhenjiang; Hidaka, Soichiro; Hiroyuki, Kato and Montrieux, Lionel (2012). Maintaining invariant traceability through bidirectional transformations. In: 34th International Conference on Software Engineering, 2-9 June 2012, Zurich, Switzerland, pp. 540–550.
- Abdelnour-Nocera, Jose and Sharp, Helen (2012). Understanding conflicts in Agile adoption through technological frames. International Journal of Sociotechnology and Knowledge Development, 4(2) pp. 29–45.
- Alebrahim, Azadeh; Tun, Thein Than; Yu, Yijun; Heisel, Maritta and Nuseibeh, Bashar (2012). An aspect-oriented approach to relating security requirements and access control. In: CAiSE'12 Forum, 28 June 2012, Gdansk, Poland.
- Ali, Raian; Solis, Carlos; Omoronyia, Inah; Salehie, Mazeiar and Nuseibeh, Bashar (2012). Social adaptation: when software gives users a voice. In: ENASE 2012: 7th International Conference Evaluation of Novel Approaches to Software Engineering , 28-30 June 2012, Wroclaw, Poland.
- Lopez, Tamara; Petre, Marian and Nuseibeh, Bashar (2012). Getting at ephemeral flaws. In: Cooperative and Human Aspects of Software Engineering (CHASE), 2012 5th International Workshop on, 2 June, 2012, Zurich.
- Sharp, Helen; Giuffrida, Rosalba and Melnik, Grigori (2012). Information flow within a dispersed agile team: a distributed cognition perspective. In: 13th International Conference on Agile Software Development: XP2012 , 20-25 May 2012, Malmö Sweden, pp. 62–76.
- Peng, Xin; Chen, Bihuan; Yu, Yijun and Zhao, Wenyun (2012). Self-tuning of software systems through goal-based feedback control loop. Journal of Systems and Software, 85(12) pp. 2707–2719.
- Petre, Marian; Baines, Chris; Baker, Michael; Copcutt, Ed; Martindale, Adam; Matharu, Taranjit and Petre Eastty, Max (2012). The interactive punching bag. ACM.
- Sardinha, Alberto; Niu, Nan; Yu, Yijun and Rashid, Awais (2012). EA-Tracer: identifying traceability links between code aspects and early aspects. In: 27th Annual ACM Symposium on Applied Computing (SAC 2012), 26-30 March 2012 , Riva del Garda (Trento) Italy.
- Richards, Michael; Petre, Marian and Bandara, Arosha (2012). Starting with Ubicomp: using the SenseBoard to introduce computing. In: 43rd ACM Technical Symposium on Computer Science Education, 29 February - 3 March 2012, Raleigh, NC.
- Yang, Hui; Willis, Alistair; De Roeck, Anne and Nuseibeh, Bashar (2012). A hybrid model for automatic emotion recognition in suicide notes. Biomedical Informatics Insights, 5(Supp 1) pp. 17–30.
- Baker, Alex; Van Der Hoek, André; Ossher, Harold and Petre, Marian (2012). Studying professional software design. IEEE Software , 29(1) pp. 28–33.
- Akiki, Pierre A.; Bandara, Arosha K. and Yu, Yijun (2012). Using interpreted runtime models for devising adaptive user interfaces of enterprise applications. In: 14th International Conference on Enterprise Information Systems (ICEIS 2012), 28 June - 1 July 2012, Wroclaw, Poland.
- Bennaceur, Amel; Issarny, Valérie; Spalazzese, Romina and Tyagi, Shashank (2012). Achieving interoperability through semantics-based technologies: the instant messaging case. In: ISWC 2012 - 11th International Semantic Web Conference, 11-15 Nov 2012, Boston, Springer-Verlag, pp. 17–33.
- Bennaceur, Amel; Johansson, Richard; Moschitti, Alessandro; Spalazzese, Romina; Sykes, Daniel; Saadi, Rachid and Issarny, Valérie (2012). Inferring affordances using learning techniques. In: Eternal Systems, Springer, pp. 79–87.
- Damian, Daniela; Petre, Marian; Miller, Mariel and Hadwin, Allyson F. (2012). Instructional strategies in the EGRET course: an international graduate forum on becoming a researcher. In: WCCCE '12 17th Western Canadian Conference on Computing Education, 4 - 5 May, 2012, Vancouver, British Columbia, Canada.
- Goulão, Miguel; Fonte, Nelson; Wermelinger, Michel and Brito e Abreu, Fernando (2012). Software evolution prediction using seasonal time analysis: a comparative study. In: 16th European Conference on Software Maintenance and Reengineering, 27-30 March 2012, Szeged, Hungary.
- Omoronyia, Inah; Pasquale, Liliana; Salehie, Mazeiar; Cavallaro, Luca; Doherty, Gavin and Nuseibeh, Bashar (2012). Caprice: a tool for engineering adaptive privacy. In: 27th IEEE/ACM International Conference on Automated Software Engineering (ASE 2012), 3-7 September 2012, Essen, Germany.
- Pasquale, Liliana; Salehie, Mazeiar; Ali, Raian; Omoronyia, Inah and Nuseibeh, Bashar (2012). On the role of primary and secondary assets in adaptive security: An application in smart grids. In: Software Engineering for Adaptive and Self-Managing Systems (SEAMS), 2012 ICSE Workshop , 4-5 June 2012, Switzerland.
- Pawar, P. S.; Rajarajan, M.; Krishnan Nair, S. and Zisman, A. (2012). Trust model for optimized cloud services. In: Trust Management VI: 6th IFIP WG 11.11 International Conference, IFIPTM 2012, Surat, India, May 21-25, 2012. Proceedings, IFIP Advances in Information and Communication Technology , Springer Berlin Heidelberg, pp. 97–112.
- Petre, Marian; Sharp, Helen and Freudenberg, Sallyann (2012). The mystery of the writing that isn’t on the wall: differences in public representations in traditional and agile software development. In: 5th International Workshop on Cooperative and Human Aspects of Software Engineering (CHASE 2012), 2-9 June 2012, Zurich, Switzerland.
- Plonka, Laura; Sharp, Helen and van der Linden, Janet (2012). Disengagement in pair programming: does it matter? In: ICSE 2012, 02-09 June 2012, Zurich, pp. 496–506.
- Salehie, Mazeiar; Pasquale, Liliana; Omoronyia, Inah; Ali, Raian and Nuseibeh, Bashar (2012). Requirements-driven adaptive security: protecting variable assets at runtime. In: 20th International Requirements Engineering Conference (RE'12), 24-28 September 2012, Chicago, USA, pp. 111–120.
- Salehie, Mazeiar; Pasquale, Liliana; Omoronyia, Inah and Nuseibeh, Bashar (2012). Adaptive security and privacy in smart grids: A software engineering vision. In: Software Engineering for the Smart Grid (SE4SG), 2012 International Workshop, 3 June 2012 , University of Zurich.
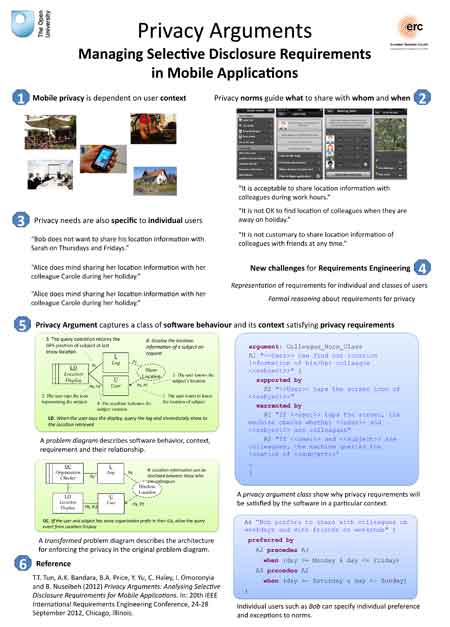
- Tun, Thein Than; Bandara, Arosha K.; Price, Blaine A.; Yu, Yijun; Haley, Charles; Omoronyia, Inah and Nuseibeh, Bashar (2012). Privacy arguments: analysing selective disclosure requirements for mobile applications. In: 20th IEEE International Requirements Engineering Conference, 24-28 September 2012 , Chicago, Illinois, pp. 131–140.
- Yang, Hui; De Roeck, Anne; Gervasi, Vincenzo; Willis, Alistair and Nuseibeh, Bashar (2012). Speculative requirements: automatic detection of uncertainty in natural language requirements. In: The 20th IEEE International Requirements Engineering Conference, 24-28 September 2012, Chicago, ILL, USA, IEEE, pp. 11–20.
2011
- Yu, Yijun; Tun, Thein and Nuseibeh, Bashar (2011). Specifying and detecting meaningful changes in programs. In: 26th IEEE/ACM International Conference On Automated Software Engineering, 6-10 Nov 2011, Lawrence, Kansas, USA , pp. 273–282.
- Yu, Yijun; Bandara, Arosha; Tun, Thein Than and Nuseibeh, Bashar (2011). Towards learning to detect meaningful changes in software. In: Proceedings of the International Workshop on Machine Learning Technologies in Software Engineering, 12 November 2011, Lawrence, Kansas, ACM, pp. 51–54.
- Bergmann, Gábor; Massacci, Fabio; Paci, Federica; Tun, Thein; Varró, Dániel and Yu, Yijun (2011). SeCMER: a tool to gain control of security requirements Evolution. In: Towards a Service-Based Internet, pp. 321–322.
- Prechett, Lutz and Petre, Marian (2011). Credibility, or why should I insist on being convinced? In: Oram, Adam and Wilson , Greg eds. Making Software: What Really Works, and Why We Believe It. Sebastapol, CA: O'Reilly Media , pp. 17–34.
- Sach, Rien; Sharp, Helen and Petre, Marian (2011). Software engineers’ perceptions of factors in motivation. In: 5th International Symposium on Empirical Software Engineering and Measurement, ESEM 2011, 22-23 September 2011, Banff, Alberta, Canada.
- Sach, Rien; Sharp, Helen and Petre, Marian (2011). What makes software engineers go that extra mile? In: 23rd Annual Psychology of Programming Interest Group 2011, 6-8 September 2011, York, UK.
- Ali, Raian; Solís, Carlos; Salehie, Mazeiar; Omoronyia, Inah; Nuseibeh, Bashar and Maalej, Walid (2011). Social sensing: when users become monitors. In: 19th ACM SIGSOFT Symposium and the 13th European Conference on Foundations of Software Engineering (ESEC/FSE 2011), 5-9 September 2011, Szeged, Hungary.
- Franqueira, Virginia N. L.; Bakalova, Zornitza; Tun, Thein Than and Daneva, Maya (2011). Towards agile security risk management in RE and beyond. In: Workshop on Empirical Requirements Engineering (EmpiRE 2011), pp. 33–36.
- Chen, Bihuan; Peng, Xin; Yu, Yijun and Zhao, Wenyun (2011). Are your sites down? Requirements-driven self-tuning for the survivability of web systems. In: 19th International Conference on Requirements Engineering, August 29 - September 2, 2011 , Trento, Italy.
- Franqueira, Virginia Nunes Leas; Tun, Thein Than; Yu, Yijun; Wieringa, Roel and Nuseibeh, Bashar (2011). Risk and argument: a risk-based argumentation method for practical security. In: 19th IEEE International Conference on Requirements Engineering, 29 Aug - 2 Sep 2011, Trento, Italy, pp. 239–248.
- Yu, Yijun; Tun, Thein; Tedeschi, Alessandra; Franqueira, Virginia N. L. and Nuseibeh, Bashar (2011). OpenArgue: supporting argumentation to evolve secure software systems. In: 2011 IEEE 19th International Requirements Engineering Conference, pp. 351–352.
- Peng, Xin; Yu, Yijun and Zhao, Wenyun (2011). Analyzing evolution of variability in a software product line: from contexts and requirements to features. Information and Software Technology, 53(7) pp. 707–721.
- Massacci, Fabio; Mylopoulos, John; Paci, Federica; Tun, Thein and Yu, Yijun (2011). An extended ontology for security requirements. In: Advanced Information Systems Engineering Workshops, pp. 622–636.
- Wermelinger, Michel; Yu, Yijun; Lozano, Angela and Capiluppi, Andrea (2011). Assessing architectural evolution: a case study. Empirical Software Engineering, 16(5) pp. 623–666.
- Benats, Guillaume; Bandara, Arosha; Yu, Yijun; Colin, Jean-Noel and Nuseibeh, Bashar (2011). PrimAndroid: privacy policy modelling and analysis for Android applications. In: IEEE International Symposium on Policies for Distributed Systems and Networks, 6-8 June 2011, Pisa, Italy.
- Borges, Rafael V.; Garcez, Artur D'Avila; Lamb, Luís C. and Nuseibeh, Bashar (2011). Learning to adapt requirements specifications of evolving systems (NIER Track). In: 33rd International Conference on Software Engineering (ICSE 2011), 21-28 May 2011, Honolulu, Hawaii, USA.
- Yang, Hui; De Roeck, Anne; Gervasi, Vincenzo ; Willis, Alistair and Nuseibeh, Bashar (2011). Analysing anaphoric ambiguity in natural language requirements. Requirements Engineering, 16(3) pp. 163–189.
- Rogers, Yvonne; Sharp, Helen and Preece, Jenny (2011). Interaction Design: Beyond Human-Computer Interaction (3rd ed). Chichester: Wiley.
- Bauer, Andreas; Jürjens, Jan and Yu, Yijun (2011). Run-time security traceability for evolving systems. The Computer Journal, 54(1) pp. 58–87.
- Aschoff, Rafael and Zisman, Andrea (2011). QoS-driven proactive adaptation of service composition. In: 9th International Conference on Service Oriented Computing (ICSOC 2011), 5-8 December 2011, Paphos, Cyprus.
- Bergmann, Gábor; Massacci, Fabio; Paci, Federica; Tun, Thein; Varró, Dániel and Yu, Yijun (2011). A tool for managing evolving security requirements. In: CAiSE Forum, 22-24 June 2011, London, pp. 49–56.
- Blair, Gordon S.; Bennaceur, Amel; Georgantas, Nikolaos; Grace, Paul; Issarny, Valérie; Nundloll, Vatsala and Paolucci, Massimo (2011). The role of ontologies in emergent middleware: supporting interoperability in complex distributed systems. In: Middleware 2011, Springer-Verlag, pp. 410–430.
- Butler, Simon; Wermelinger, Michel; Yu, Yijun and Sharp, Helen (2011). Improving the tokenisation of identifier names. In: ECOOP 2011 – Object-Oriented Programming (Mira, Mezini ed.), Lecture Notes in Computer Science, Springer Verlag, pp. 130–154.
- Butler, Simon; Wermelinger, Michel; Yu, Yijun and Sharp, Helen (2011). Mining Java Class Naming Conventions. In: 27th IEEE International Conference on Software Maintenance, 25-30 September 2011, Williamsburg, VA, USA, pp. 93–102.
- Chen, Bihuan; Peng, Xin; Yu, Yijun and Zhao, Wenyun (2011). Survivability-oriented self-tuning of web systems. In: 20th International World Wide Web Conference, 28 March-1 April 2011, Hyderabad, India.
- Dilshener, Tezcan and Wermelinger, Michel (2011). Relating Developers’ Concepts and Artefact Vocabulary in a Financial Software Module. In: 27th IEEE International Conference on Software Maintenance, 25-30 September 2011, Williamsburg VA, USA.
- Ferreira, Jennifer; Sharp, Helen and Robinson, Hugh (2011). User experience design and agile development: managing cooperation through articulation work. Software: Practice and Experience, 41(9) pp. 963–974.
- González, Antonio; Therón, Roberto; García-Peñalvo, Francisco; Wermelinger, Michel and Yu, Yijun (2011). Maleku: an evolutionary visual software analytics tool for providing insights into software evolution. In: 27th International Conference on Software Maintenance, 25-30 September 2011, Williamsburg VA, USA.
- Grace, Paul; Georgantas, Nikolaos; Bennaceur, Amel; Blair, Gordon S.; Chauvel, Franck; Issarny, Valérie; Paolucci, Massimo; Saadi, Rachid; Souville, Betrand and Sykes, Daniel (2011). The CONNECT architecture. In: Bernardo, Marco and Issarny, Valérie eds. Formal Methods for Eternal Networked Software Systems. Lecture Notes in Computer Science (6659). Berlin: Springer, pp. 27–52.
- Heyman, Thomas; Yskout, Koen; Scandariato, Riccardo; Schmidt, Holger and Yu, Yijun (2011). The Security Twin Peaks. In: Engineering Secure Software and Systems - Third International Symposium, 09-10 Feb 2011, Madrid, Spain.
- Hughes, Craig; Wermelinger, Michel and Holland, Simon (2011). Sound Spheres: A Design Study of the Articulacy of a Non-Contact Finger Tracking Virtual Musical Instrument. In: 8th Sound and Music Computing Conference, 6-9 July 2011, Padova, Italy.
- Hundhausen, Christopher; Fairbrother, Dana and Petre, Marian (2011). The "prototype walkthrough": a studio-based learning activity for human-computer interaction courses. In: ICER: 7th International Computing Education Research Workshop, 8-9 Aug 2011, Providence, RI, USA.
- Issarny, Valérie; Bennaceur, Amel and Bromberg, Yérom-David (2011). Middleware-layer connector synthesis: beyond state of the art in middleware interoperability. In: Bernardo, Marco and Issarny, Valérie eds. Formal Methods for Eternal Networked Software Systems: 11th International School on Formal Methods for the Design of Computer, Communication and Software Systems, SFM 2011, Bertinoro, Italy, June 13-18, 2011. Advanced Lectures. Lecture Notes in Computer Science (6659). Berlin Heidelberg: Springer, pp. 217–255.
- Mancini, Clara; Rogers, Yvonne; Thomas, Keerthi; Joinson, Adam; Price, Blaine; Bandara, Arosha; Jedrzejczyk, Lukasz and Nuseibeh, Bashar (2011). In the best families: tracking and relationships. In: 29th International ACM Conference on Human Factors in Computing Systems, ACM CHI 2011, 07-12 May 2011, Vancouver, Canada, pp. 2419–2428.
- Montrieux, Lionel; Wermelinger, Michel and Yu, Yijun (2011). Challenges in Model-Based Evolution and Merging of Access Control Policies. In: Joint 12th International Workshop on Principles on Software Evolution and 7th ERCIM Workshop on Software Evolution, 5-6 Sep 2011, Szeged, Hungary.
- Montrieux, Lionel; Wermelinger, Michel and Yu, Yijun (2011). Tool support for UML-based specification and verification of role-based access control properties. In: 8th joint meeting of the European Software Engineering Conference and the ACM SIGSOFT Symposium on the Foundations of Software Engineering , 4-9 Sep 2011, Szeged, Hungary.
- Peng, Xin; Xing, Zhenchang; Tan, Xi; Yu, Yijun and Zhao, Wenyun (2011). Iterative context-aware feature location (NIER track). In: 33rd International Conference on Software Engineering (ICSE 2011), 21-28 May 2011, Honolulu, Hawaii, USA.
- Plonka, Laura; Segal, Judith; Sharp, Helen and van der Linden, Janet (2011). Collaboration in Pair Programming: driving and switching. In: XP 2011 : 12th International Conference on Agile Software Development, 10-13 May 2011.
- Sharp, Helen and Yu, Yijun (2011). Analysing requirements in a case study of pairing. In: Workdhop on Agile Requirements Engineering (Agile RE) at ECOOP 2011 25th European Conference on Object-Oriented Programming, 26 July 2011, Lancaster, UK.
- Trew, Tim; Botterweck, Goetz and Nuseibeh, Bashar (2011). A reference architecture for consumer electronics products and its application in requirements engineering. In: Avgeriou, P.; Grundy, J.; Hall, J. G.; Lago, P. and Mistrik, I. eds. Relating Software Requirements and Architectures. Heidelberg, Germany and London, UK and New York, USA: Springer, pp. 203–231.
- Wermelinger, Michel and Yu, Yijun (2011). Some issues in the 'archaeology' of software evolution. In: Fernandes, J. M.; Lämmel, R.; Visser, J. and Saraiva, J. eds. Generative and Transformational Techniques in Software Engineering III. Lecture Notes in Computer Science (6491). Springer, pp. 426–445.
- Yu, Yijun; Petre, Marian and Tun, Thein Than (2011). Miki: a wiki for synchronous modeling of software requirements. In: 4th FlexiTools workshop @ ICSE 2011, 22 May 2011, Waikiki, Honolulu, Hawaii.
2010
- Barroca, Leonor; Rapanotti, Lucia; Petre, Marian; Vargas-Vera, Maria and Reeves, Ahmad (2010). Developing research degrees online. In: International Conference on Education, Research and Innovation, 15-17 Nov 2010, Madrid, Spain.
- Petre, Marian; van der Hoek, André and Baker, Alex (2010). Editorial. Design Studies, 31(6) pp. 533–544.
- Bandara, Arosha; Shinpei, Hayashi; Jurjens, Jan; Kaiya, Haruhiko; Kubo, Atsuto; Laney, Robin; Mouratidis, Haris; Nhlabatsi, Armstrong; Nuseibeh, Bashar; Tahara, Yasuyuki; Tun, Thein; Washizaki, Hironori; Yoshioka, Nobukazi and Yu, Yijun (2010). Security patterns: comparing modeling approaches. In: Mouratidis, Haris ed. Software Engineering for Secure Systems: Industrial and Research Perspectives. Hershey, PA: IGI Global, pp. 75–111.
- Freudenberg, SallyAnn and Sharp, Helen (2010). The top 10 burning research questions from practitioners. IEEE Software, 27(5) pp. 8–9.
- Sach, Rien; Petre, Marian and Sharp, Helen (2010). The use of MBTI in software engineering. In: 22nd Annual Psychology of Programming Interest Group 2010, 19-22 September 2010, Universidad Carlos III de Madrid.
- Sach, Rien; Sharp, Helen and Petre, Marian (2010). Continued Involvement in Software Development: Motivational Factors. In: Proceedings of the 2010 ACM-IEEE International Symposium on Empirical Software Engineering and Measurement, ACM, pp. 331–334.
- Jedrzejczyk, Lukasz; Price, Blaine A.; Bandara, Arosha and Nuseibeh, Bashar (2010). “Privacy-shake”: a haptic interface for managing privacy settings in mobile location sharing applications. In: MobileHCI '10: Proceedings of the 12th International Conference on Human Computer Interaction with Mobile Devices and Services, 7-10 September 2010, Libon, Portugal, ACM, pp. 411–412.
- Niu, Nan; Savolainen, Juha and Yu, Yijun (2010). Variability modeling for product line viewpoints integration. In: 34th Annual IEEE Computer Software and Applications Conference, 19-23 July 2010, Seoul, South Korea.
- Mahfouz, Ayman; Barroca, Leonor; Laney, Robin and Nuseibeh, Bashar (2010). Requirements-driven design of service-oriented interactions. IEEE Software, 27(6) pp. 25–32.
- Jedrzejczyk, Lukasz; Price, Blaine A.; Bandara, Arosha K. and Nuseibeh, Bashar (2010). On the impact of real-time feedback on users' behaviour in mobile location-sharing applications. In: SOUPS '10: Proceedings of the Sixth Symposium on Usable Privacy and Security, 14-16 July 2010, ACM, pp. 1–12.
- Tun, Thein Than; Yu, Yijun; Haley, C. and Nuseibeh, B. (2010). Model-Based argument analysis for evolving security requirements. In: Fourth International Conference on Secure Software Integration and Reliability Improvement (SSIRI), 2010, IEEE, pp. 88–97.
- Nuseibeh, Bashar and Zave, Pamela eds. (2010). Software Requirements and Design: The Work of Michael Jackson. Good Friends Publishing Company.
- Spanoudakis, George and Zisman, Andrea (2010). Discovering services during service-based system design using UML. IEEE Transactions on Software Engineering, 36(3) pp. 371–389.
- Mancini, Clara; Rogers, Yvonne; Bandara, Arosha; Coe, Tony; Jedrzejczyk, Lukasz; Joinson, Adam; Price, Blaine; Thomas, Keerthi and Nuseibeh, Bashar (2010). Contravision: Exploring users' reactions to futuristic technology. In: Proceedings of the 28th International Conference on Human factors in computing systems, 10-15 April 2010, Atlanta Georgia, USA, pp. 153–162.
- Price, Blaine A.; Mancini, Clara; Rogers, Yvonne; Bandara, Arosha K.; Coe, Tony; Joinson, Adam N.; Lay, Jeffery A. and Nuseibeh, Bashar (2010). ContraVision: presenting contrasting visions of future technology. In: 28th International Conference on Human Factors in Computing Systems, 10-15 Apr 2010, Atlanta, GA, USA, pp. 4759–4764.
- Butler, Simon; Wermelinger, Michel; Yu, Yijun and Sharp, Helen (2010). Exploring the Influence of Identifier Names on Code Quality: An empirical study. In: 14th European Conference on Software Maintenance and Reengineering, 15-18 March 2010, Madrid, Spain, pp. 156–165.
- Bennaceur, Amel; Blair, Gordon; Chauvel, Franck; Gang, Huang; Georgantas, Nikolaos; Grace, Paul; Howar, Falk; Inverardi, Paola; Issarny, Valrie; Paolucci, Massimo; Pathak, Animesh; Spalazzese, Romina; Steffen, Bernhard and Souville, Bertrand (2010). Towards an architecture for runtime interoperability. In: Leveraging Applications of Formal Methods, Verification, and Validation, Springer, pp. 206–220.
- Calo, Seraphin B.; Karat, Clare-Marie; Karat, John; Lobo, Jorge; Craven, Robert; Lupu, Emil ; Ma, Jiefei; Russo, Alessandra; Sloman, Morris and Bandara, Arosha (2010). Policy technologies for security management in coalition networks. In: Verma, Dinesh ed. Network Science for Military Coalition Operations: Information Exchange and Interaction. Premier Reference Source. Pennsylvania, USA: IGI Global, pp. 146–173.
- Hundhausenm , Christopher; Fairbrother, Dana and Petre, Marian (2010). The “prototype walkthrough”: a studio-based learning activity for the next generation of HCI education. In: Next Generation of HCI and Education: CHI 2010 Workshop on UI Technologies and Educational Pedagogy, 11 Apr 2010, Atlanta, GA.
- Lozano Rodriguez, Angela and Wermelinger, Michel (2010). Tracking clones' imprint. In: 4th International Workshop on Software Clones, 8 May 2010, Cape Town, South Africa.
- Montrieux, Lionel; Jürjens, Jan; Haley, Charles; Yu, Yijun; Schobbens, Pierre-Yves and Toussaint, Hubert (2010). Tool support for code generation from a UMLsec property. In: ASE'10 - 25th International Conference on Automated Software Engineering, 20-24 September 2010, Antwerp, Belgium.
- Nhlabatsi, Armstrong; Nuseibeh, Bashar and Yu, Yijun (2010). Security requirements engineering for evolving software systems: a survey. International Journal of Secure Software Engineering (IJSSE), 1(1) pp. 54–73.
- Peng, Xin; Chen, Bihuan; Yu, Yijun and Zhao, Wenyun (2010). Self-tuning of software systems through goal-based feedback loop control. In: 18th IEEE International Requirements Engineering Conference (RE 2010), 27September-1 October 2010, Sydney, Australia.
- Petre, Marian (2010). Mental imagery and software visualization in high-performance software development teams. Journal of Visual Languages & Computing, 21(3) pp. 171–183.
- Robinson, Hugh and Sharp, Helen (2010). Collaboration, communication and coordination in Agile software development practice. In: Mistrík, Ivan; Grundy, John; Hoek, André and Whitehead, Jim eds. Collaborative Software Engineering. Berlin/Heidelberg: Springer, pp. 93–108.
- Sharp, Helen and Robinson, Hugh (2010). Three ‘c’s of agile practice: collaboration, coordination and communication. In: Dingsøyr, Torgeir; Dybå, Tore and Moe, Nils Brede eds. Agile Software Development: Current Research and Future Directions. Berlin: Springer, pp. 61–85.
- Siveroni, Igor; Zisman, Andrea and Spanoudakis, George (2010). A UML-based static verification framework for security. Requirements Engineering , 15(1) pp. 95–118.
- Supakkul, Sam; Hill, Tom; Chung, Lawrence; Tun, Thein Than and do Prado Leite, Julio Cesar Sampaio (2010). An NFR pattern approach to dealing with NFRs. In: 2010 18th IEEE International Requirements Engineering Conference, pp. 179–188.
- Wermelinger, Michel and Bandara, Arosha (2010). Commentary on ‘Software architectures and mobility: A roadmap’. Journal of Systems and Software, 83(6) pp. 899–901.
- Yang, Hui; De Roeck, Anne; Gervasi, Vincenzo; Willis, Alistair and Nuseibeh, Bashar (2010). Extending Nocuous Ambiguity Analysis for Anaphora in Natural Language Requirements. In: 18th International IEEE Requirements Engineering Conference (RE'10), 27 Sep - 1 Oct 2010, Sydney, Australia, pp. 25–34.
- Yang, Hui; De Roeck, Anne; Willis, Alistair and Nuseibeh, Bashar (2010). A methodology for automatic identification of nocuous ambiguity. In: The 23rd International Conference on Computational Linguistics (Coling 2010), 23-27 Aug 2010, Beijing, China, pp. 1218–1226.
- Yang, Hui; Willis, Alistair; De Roeck, Anne and Nuseibeh, Bashar (2010). Automatic detection of nocuous coordination ambiguities in natural language requirements. In: Proceedings of the IEEE/ACM international conference on Automated software engineering, ACM, pp. 53–62.
2009
- Mahfouz, Ayman; Barroca, Leonor; Laney, Robin and Nuseibeh, Bashar (2009). Requirements-driven collaborative choreography customization. In: 7th International Joint Conference on Service Oriented Computing, 23-27 November 2009, Stockholm, Sweden.
- Overton, Jerry; Hall, Jon; Rapanotti, Lucia and Yu, Yijun (2009). Towards a problem oriented engineering theory of pattern-oriented analysis and design. In: Computer Software and Applications Conference, 2009. COMPSAC '09. 33rd Annual IEEE International pp. 255–260.
- Gacitua, R.; Ma, L.; Nuseibeh, B.; Piwek, P.; De Roeck, A.; Rouncefield, M.; Sawyer, P.; Willis, A. and Yang, H. (2009). Making tacit requirements explicit. In: Second International Workshop on Managing Requirements Knowledge (MaRK’09) , 1 Sep 2009, Altanta, USA.
- Ma, Lin; Nuseibeh, Bashar; Piwek, Paul; De Roeck, Anne and Willis, Alistair (2009). On presuppositions in requirements. In: 2009 Second International Workshop on Managing Requirements Knowledge (MaRK'09), 1 September 2009, Atlanta, Georgia, USA.
- Nuseibeh, Bashar; Haley, Charles B. and Foster, Craig (2009). Securing the skies: In requirements we trust. Computer, 42(9) pp. 64–72.
- Tun, Thein Than; Trew, Tim; Jackson, Michael; Laney, Robin and Nuseibeh, Bashar (2009). Specifying features of an evolving software system. Software: Practice and Experience, 39(11) pp. 973–1002.
- Petre, Marian (2009). Insights from expert software design practice. In: 7th joint meeting of the European Software Engineering Conference (ESEC) and the ACM SIGSOFT Symposium on the Foundations of Software Engineering (FSE), 24-28 August 2009, Amsterdam, The Netherlands, pp. 233–242.
- Tun, Thein; Jackson, Michael; Laney, Robin; Nuseibeh, Bashar and Yu, Yijun (2009). Are your lights off? Using problem frames to diagnose system failures. In: 17th IEEE International Requirements Engineering Conference, 31 August - 4 September 2009, Atlanta, Georgia, USA.
- Thomas, Keerthi; Mancini, Clara; Jedrzejczyk, Lukasz; Bandara, Arosha K.; Joinson, Adam; Price, Blaine A.; Rogers, Yvonne and Nuseibeh, Bashar (2009). Studying location privacy in mobile applications: 'predator vs. prey' probes. In: Proceedings of the 5th Symposium on Usable Privacy and Security, 15-17 July 2009, California, ACM, p. 1.
- Govaerts, John; Bandara, Arosha and Curran, Kevin (2009). A formal logic approach to firewall packet filtering analysis and generation. Artificial Intelligence Review, 29(3-4) pp. 223–248.
- Nhlabatsi, Armstrong; Laney, Robin and Nuseibeh, Bashar (2009). Feature interaction as a context sharing problem. In: International Conference on Feature Interactions, 11-12 June, University of Lisbon, Portugal.
- Niu, Nan; Yu, Yijun; González-Baixauli, Bruno; Ernst, Neil; Leite, Julio Cesar Sampaio do Prado and Mylopoulos, John (2009). Aspects across Software Life Cycle: A Goal-Driven Approach. In: Katz, Shmuel; Ossher, Harold; France, Robert and Jézéquel, Jean-Marc eds. Transactions on Aspect-Oriented Software Development VI. Lecture Notes in Computer Science, VI. Springer, pp. 83–110.
- Hall, Tracy; Baddoo, Nathan; Beecham, Sarah; Robinson, Hugh and Sharp, Helen (2009). A systematic review of theory use in studies investigating the motivations of software engineers. ACM Transactions on Software Engineering and Methodology, 18(3), article no. 10.
- Robinson, Hugh and Sharp, Helen (2009). The emergence of object-oriented technology: the role of community. Behaviour & Information Technology, 28(3) pp. 211–222.
- Wermelinger, Michel; Yu, Yijun and Strohmaier, Markus (2009). Using formal concept analysis to construct and visualise hierarchies of socio-technical relations. In: Proceedings of the 31st International Conference on Software Engineering, Companion Volume, 18-24 May 2009, Vancouver, IEEE.
- Craven, Robert; Lobo, Jorge; Lupu, Emil C.; Ma, Jiefei; Russo, Alessandra; Bandara, Arosha K.; Calo, Seraphin and Sloman, Morris (2009). Expressive policy analysis with enhanced system dynamicity. In: ACM Symposium on Information, Computer and Communications Security (ASIACCS 2009), 10-12 March 2009, Sydney, Australia, ACM.
- Wang, Yiqiao; Mcilraith, Sheila A.; Yu, Yijun and Mylopoulos, John (2009). Monitoring and diagnosing software requirements. Automated Software Engineering, 16(1) pp. 3–35.
- Jirapanthong, Waraporn and Zisman, Andrea (2009). XTraQue: traceability for product line systems. Software and Systems Modeling, 8(1) pp. 117–144.
- Sharp, Helen; Robinson, Hugh and Petre, Marian (2009). The role of physical artefacts in agile software development: Two complementary perspectives. Interacting with Computers, 21(1-2) pp. 108–116.
- Yu, Yijun; Niu, Nan; González-Baixauli, Bruno; Mylopoulos, John; Easterbrook, Steve and Leite, Julio Cesar Sampaio do Prado (2009). Requirements engineering and aspects. In: Lyytinen, Kalle; Loucopoulos, Pericles; Mylopoulos, John and Robinson, Bill eds. Design Requirements Engineering: A Ten-Year Perspective. Lecture Notes in Business Information Processing, 14. Springer Berlin Heidelberg, pp. 432–452.
- Bandara, A. K.; Kakas, A. C.; Lupu, E. C. and Russo, A. (2009). Using argumentation logic for firewall configuration management. In: IFIP/IEEE International Symposium on Integrated Network Management (IM '09), 1-5 June 2009, Long Island, USA, pp. 180–187.
- Bennaceur, Amel; Singh, Pushpendra; Raverdy, Pierre-Guillaume and Issarny, Valerie (2009). The iBICOOP middleware: enablers and services for emerging pervasive computing environments. In: 2009 IEEE International Conference on Pervasive Computing and Communications, IEEE.
- Butler, Simon; Wermelinger, Michel; Yu, Yijun and Sharp, Helen (2009). Relating identifier naming flaws and code quality: An empirical study. In: 16th Working Conference on Reverse Engineering, 13-16 October 2009, Lille, France.
- Charalambides, M.; Flegkas, P.; Pavlou, G.; Rubio-Loyola, J.; Bandara, A. K.; Lupu, E. C.; Russo, A.; Dulay, N. and Sloman, M. (2009). Policy conflict analysis for diffserv quality of service management. IEEE Transactions on Network and Service Management, 6(1) pp. 15–30.
- Classen, Andreas; Heymans, Patrick; Tun, Thein and Nuseibeh, Bashar (2009). Towards safer composition. In: 2009 31st International Conference on Software Engineering - Companion Volume, pp. 227–230.
- Corapi, Domenico; Ray, Oliver; Russo, Alessandra; Bandara, Arosha and Lupu, Emil (2009). Learning rules from user behaviour. In: Artificial Intelligence Applications and Innovations III: Proceedings of the 5TH IFIP Conference on Artificial Intelligence Applications and Innovations (AIAI '2009), 23-25 April 2009, Thessaloniki, Greece, pp. 459–468.
- Haley, Debra; Thomas, Pete; Petre, Marian and De Roeck, Anne (2009). Human fallibility: How well do human markers agree? In: The Eleventh Australasian Computing Education Conference (ACE2009), 20-23 Jan 2009, Wellington, New Zealand.
- Mahfouz, Ayman; Barroca, Leonor; Laney, Robin and Nuseibeh, Bashar (2009). From organizational requirements to service choreography. In: 2009 IEEE Congress on Services (SERVICES 2009), 6-10 July, 2009, Los Angeles, CA, USA.
- Mancini, Clara; Rogers, Yvonne; Jedrzejczyk, Lukasz; Thomas, Keerthi; Price, Blaine; Joinson, Adam; Bandara, Arosha and Nuseibeh, Bashar (2009). A multi-pronged empirical approach to mobile privacy investigation. In: Workshop on Mobile User Experience Research: Challenges, Methods & Tools. 27th ACM International Conference on Human Factors in Computing Systems, ACM CHI 2009, 4-9 Apr 2009, Boston, USA.
- Mancini, Clara; Thomas, Keerthi; Rogers, Yvonne; Price, Blaine A.; Jedrzejczyk, Lukazs; Bandara, Arosha K.; Joinson, Adam N. and Nuseibeh, Bashar (2009). From spaces to places: Emerging contexts in mobile privacy. In: Proceedings of the 11th International conference on Ubiquitous computing, 30 Sept - 3 Oct 2009, Orlando, Florida, USA, ACM, pp. 1–10.
- Ostacchini, Ireo and Wermelinger, Michel (2009). Managing assumptions during agile development. In: Fourth ICSE Workshop on Sharing and Reusing Architectural Knowledge, 16 May 2009, Vancouver, Canada.
- Sharp, Helen; Baddoo, Nathan; Beecham, Sarah; Hall, Tracy and Robinson, Hugh (2009). Models of motivation in software engineering. Information and Software Technology, 51(1) pp. 219–233.
- Tun, Thein; Boucher, Quentin; Classen, Andreas; Hubaux, Arnaud and Heymans, Patrick (2009). Relating requirements and feature configurations: a systematic approach. In: Proceedings of the 13th International Software Product Line Conference, 24-28 Aug 2009, Carnegie Mellon University Pittsburgh, PA, USA, Carnegie Mellon University, pp. 201–210.
- Tun, Thein; Chapman, Rod; Haley, Charles; Laney, Robin and Nuseibeh, Bashar (2009). A framework for developing feature-rich software systems. In: 16th Annual IEEE International Conference and Workshop on the Engineering of Computer Based Systems (ECBS 2009), 14-16 April 2009, San Francisco, California, USA.
- Tun, Thein and Heymans, Patrick (2009). Concerns and their separation in feature diagram languages: An informal survey. In: Workshop on Scalable Modelling Techniques for Software Product Lines, August 24, 2009, San Francisco, CA, USA.
- Tun, Thein Than; Yu, Yijun; Laney, Robin and Nuseibeh, Bashar (2009). Early identification of problem interactions: A tool-supported approach. In: Glinz, Martin and Heymans, Patrick eds. Requirements Engineering: Foundation for Software Quality, 15th International Working Conference. Lecture Notes in Computer Science (5512). Germany: Springer Verlag, pp. 74–88.
2008
- Jackson, Michael (2008). Automated software engineering: supporting understanding. Automated Software Engineering, 15(3-4) pp. 275–281.
- Lozano, Angela and Wermelinger, Michel (2008). Assessing the effect of clones on changeability. In: Proceedings of the 24th IEEE International Conference on Software Maintenance, 28 Sept - 4 Oct 2008, Beijing, China, IEEE, pp. 227–236.
- Sharp, Helen and Robinson, Hugh (2008). Collaboration and co-ordination in mature eXtreme programming teams. International Journal of Human-Computer Studies, 66(7) pp. 506–518.
- Wermelinger, Michel; Yu, Yijun and Lozano Rodriguez, Angela (2008). Design Principles in Architectural Evolution: a Case Study. In: Proceedings of the 24th IEEE International Conference on Software Maintenance, 28 Sept - 4 Oct 2008, Beijing, China, IEEE, pp. 396–405.
- Lozano Rodriguez, Angela; Wermelinger, Michel and Nuseibeh, Bashar (2008). Evaluating the relation between changeability decay and the characteristics of clones and methods. In: 4th International ERCIM Workshop on Software Evolution and Evolvability, 15-16 September 2008, L'Aquila, Italy, IEEE, pp. 100–109.
- Mahfouz, Ayman; Barroca, Leonor; Laney, Robin and Nuseibeh, Bashar (2008). Customizing choreography: Deriving conversations from organizational dependencies. In: 12th IEEE International Enterprise Distributed Object Computing Conference (EDOC 2008), 15-19 September 2008, München, Germany.
- Haley, Charles B. and Nuseibeh, Bashar (2008). Bridging requirements and architecture for systems of systems. In: 3rd International Symposium on Information Technology (ITSIM'08), 26-28 Aug 2008, Kuala Lumpur, Malaysia.
- Beecham, Sarah; Baddoo, Nathan; Hall, Tracy; Robinson, Hugh and Sharp, Helen (2008). Motivation in software engineering: a systematic literature review. Information and Software Technology, 50(9-10) pp. 860–878.
- Hall, Tracy; Sharp, Helen; Beecham, Sarah; Baddoo, Nathan and Robinson, Hugh (2008). What do we know about developer motivation? IEEE Software, 25(4) pp. 92–94.
- Yu, Yijun; Lapouchnian, Alexei; Liaskos, Sotirios; Mylopoulos, John and Leite, Julio C. S. P. (2008). From goals to high-variability software design. In: Proceedings of Foundations of Intelligent Systems: 17th International Symposium, ISMIS 2008, Springer, pp. 1–16.
- Yu, Yijun; Leite, Julio Cesar Sampaio do Prado; Lapouchnian, Alexei and Mylopoulos, John (2008). Configuring features with stakeholder goals. In: Proceedings of the 2008 ACM Symposium on Applied Computing (SAC), 16-20 Mar 2008, Fortaleza, Ceara, Brazil.
- Haley, Charles B.; Laney, Robin; Moffett, Jonathan D. and Nuseibeh, Bashar (2008). Security Requirements Engineering: A Framework for Representation and Analysis. IEEE Transactions on Software Engineering, 34(1) pp. 133–153.
- Bandara, A. K.; Damianou, N.; Lupu, E. C. and Sloman, M. (2008). Policy based management. In: Bergstra, J. and Burgess, M. eds. Handbook of Network and System Administration. Elsevier, pp. 507–564.
- Classen, Andreas; Laney, Robin; Tun, Thein Than; Heymans, Patrick and Hubaux, Arnaud (2008). Using the event calculus to reason about problem diagrams. In: Proceedings of the 3rd international workshop on applications and advances of problem frames, May 2008, Leipzig, Germany.
- Ellims, Mike; Ince, Darrel and Petre, Marian (2008). The effectiveness of t-way test data generation. In: Computer Safety, Reliability, and Security: 27th International Conference, SAFECOMP 2008, Newcastle upon Tyne, UK, 22-25 September 2008, Berlin.
- Ernst, Neil; Mylopoulos, John; Yu, Yijun and Ngyuen, Tien T. (2008). Supporting requirements model evolution throughout the system life-cycle. In: 16th IEEE International Requirements Engineering Conference, 08-12 Sep 2008, Barcelona, Spain.
- Fernandez-Ramil, Juan; Lozano, Angela; Wermelinger, Michel and Capiluppi, Andrea (2008). Empirical studies of open source evolution. In: Mens, Tom and Demeyer, Serge eds. Software Evolution. Berlin: Springer, pp. 263–288.
- Haley, Charles B; Laney, Robin; Moffett, Jonathan D and Nuseibeh, Bashar (2008). Arguing satisfaction of security requirements. In: Nemati, Hamid ed. Information Security and Ethics: Concepts, Methodologies, Tools, and Applications, Volume 4. Information Science Reference.
- Jurjens, Jan; Schreck, Jörg and Yu, Yijun (2008). Automated analysis of permission-based security using UMLsec (TOOL DEMO). In: ETAPS 2008 , 29 March - 6 April 2008, Budapest, Hungary.
- Minocha, Shailey; Petre, Marian and Roberts, Dave (2008). Using wikis to simulate distributed requirements development in a software engineering course. International Journal of Engineering Education, 24(4) pp. 689–704.
- Richards, Mike; Price, Blaine A. and Nuseibeh, Bashar (2008). Placing computer security at the heart of learning. Progress in Informatics, 5(2008) pp. 91–98.
- Tun, Thein Than; Hall, Jon G.; Rapanotti, Lucia; Cox, Karl and Jin, Zhi (2008). 3rd international workshop on advances and applications of problem frames. In: International Conference on Software Engineering, 10 May 2008, Leipzig, Germany, pp. 1029–1030.
- Yu, Yijun; Jurjens, Jan and Mylopoulos, John (2008). Traceability for the maintenance of secure software. In: 2008 IEEE International Conference on Software Maintenance, p. 297.
- Yu, Yijun; Kaiya, Haruhiko; Washizaki, Hironori; Xiong, Yingfei; Hu, Zhenjiang and Yoshioka, Nobukazu (2008). Enforcing a security pattern in stakeholder goal models. In: 4th ACM Workshop on Quality of Protection in conjunction with CCS '08, 15th ACM Conference on Computer and Communications Security, 27-31 October 2008, Alexandria, VA, USA.
- Yu, Yijun and Wermelinger, Michel (2008). Graph-centric tools for understanding the evolution and relationships of software structures. In: 2008 15th Working Conference on Reverse Engineering, p. 329.
2007
- Wang, Yiqiao; McIlraith, Sheila A.; Yu, Yijun and Mylopoulos, John (2007). An automated approach to monitoring and diagnosing requirements. In: 22nd IEEE/ACM international conference on Automated software engineering, 7-9 Nov 2007, Atlanta, Georgia, USA.
- Salifu, Mohammed; Yu, Yijun and Nuseibeh, Bashar (2007). Specifying Monitoring and Switching Problems in Context. In: 15th IEEE International Requirements Engineering Conference (RE 2007), 15 Oct - 19 Oct 2007, Delhi, India.
- Haley, Debra; Thomas, Pete; De Roeck, Anne and Petre, Marian (2007). Seeing the whole picture: evaluating automated assessment systems. Innovation in Teaching And Learning in Information and Computer Sciences, 6(4) pp. 203–224.
- Lapouchnian, Alexei; Yu, Yijun and Mylopoulos, John (2007). Requirements-driven design and configuration management of business processes. In: ed. Business process management. Lecture Notes in Computer Science, 4714/2. Berlin: Springer.
- Hall, Jon G.; Rapanotti, Lucia and Jackson, Michael (2007). Problem Oriented Software Engineering: A design-theoretic approach for software engineering. In: Proceedings of the 11th IEEE International Requirements Engineering Conference, pp. 181–187.
- Hall, Jon G.; Rapanotti, Lucia and Jackson, Michael (2007). Problem oriented software engineering: A design-theoretic framework for software engineering. In: Proceedings of the Fifth IEEE International Conference on Software Engineering and Formal Methods (SEFM 2007), 10 -14 September 2007, London, UK.
- Petre, Marian and Blackwell, Alan (2007). Children as unwitting end-user programmers. In: IEEE Symposium on Visual Languages and Human-Centric Computing, 23-27 Sep 2007, Coeur d'Alène, Idaho.
- Yu, Yijun; Lu, Jianguo; Ramil, Juan F. and Yuan, Phil (2007). Comparing Web Services with other Software Components. In: 2007 IEEE International Conference on Web Services (ICWS 2007), July 9-13, 2007, Salt Lake City, Utah, USA.
- Bandara, A. K.; Russo, A. and Lupu, E. C. (2007). Towards learning privacy policies. In: 8th IEEE International Workshop on Policies for Distributed Systems and Networks (Western Ontario, University of ed.), 13-15 June, Bologna, Italy, IEEE Computer Society, p. 274.
- Robinson, Hugh; Segal, Judith and Sharp, Helen (2007). Ethnographically-informed empirical studies of software practice. Information and Software Technology, 49(6) pp. 540–551.
- Capiluppi, A.; Fernandez-Ramil, J.; Higman, J.; Sharp, H.C. and Smith, N. (2007). An Empirical Study of the Evolution of an Agile-Developed Software System. In: 29th International Conference on Software Engineering, 20-26 May 2007, Minneapolis, USA.
- Nocera, Jose Abdelnour; Dunckley, Lynne and Sharp, Helen (2007). An approach to the evaluation of usefulness as a social construct using technological frames. International Journal of Human-Computer Interaction, 22(1-2) pp. 153–172.
- Classen, Andreas; Heymans, Patrick; Laney, Robin; Nuseibeh, Bashar and Tun, Thein Than (2007). On the structure of problem variability: From feature diagrams to problem frames. In: Proceedings of International workshop on Variability Modeling of Software-intensive Systems, 16-18 January 2007, Limerick, Ireland, pp. 109–118.
- Oliveira, Cristóvão and Wermelinger, Michel (2007). A model-driven approach to extract views from an architecture description language. In: Proceedings of the Working IEEE/IFIP Conference on Software Architecture (WICSA'07), 6-9 January 2007, Mumbai, India.
- Salifu, Mohammed; Nuseibeh, Bashar; Rapanotti, Lucia and Tun, Thein Than (2007). Using problem descriptions to represent variabilities for context-aware applications. In: Proceedings of 1st International workshop on Variability Modeling of Software-intensive Systems (VaMoS 2007), 16-18 Jan 2007, Limerick, Ireland, pp. 149–156.
- Sharp, Helen; Rogers, Yvonne and Preece, Jenny (2007). Interaction Design: Beyond Human-Computer Interaction. Second Edition. UK: John Wiley.
- Haley, Debra; Thomas, Pete; De Roeck, Anne and Petre, Marian (2007). Measuring improvement in latent semantic analysis-based marking systems: using a computer to mark questions about HTML. In: ACM 9th International Australasian Computing Education Conference, 30 Jan - 02 Feb 2007, Ballarat, Victoria, Australia.
- Heath, Tom; Motta, Enrico and Petre, Marian (2007). Computing word-of-mouth trust relationships in social networks from Semantic Web and Web 2.0 data sources. In: The 4th European Semantic Web Conference (ESWC 2007), 3-7Jun e2007, Innsbruck, Austria.
- Jackson, Michael (2007). Testing the machine in the world. In: Bin, Eyal; Ziv, Avi and Ur, Shmuel eds. Hardware and Software, Verification and Testing. Lecture Notes in Computer Science; Programming and Software Engineering (Vol. 4383). Springer, pp. 198–203.
- Jürjens, Jan and Yu, Yijun (2007). Tools for model-based security engineering: models vs. code. In: 22nd IEEE/ACM International Conference on Automated Software Engineering, 5-9 November 2007, Atlanta, Georgia, USA.
- Laney, Robin; Tun, Thein Than; Jackson, Michael and Nuseibeh, Bashar (2007). Composing features by managing inconsistent requirements. In: Proceedings of 9th International Conference on Feature Interactions in Software and Communication Systems (ICFI 2007), 3-5 September 2007, Grenoble, France, pp. 141–156.
- Lu, Jianguo and Yu, Yijun (2007). Web service search: who, when, what, and how. In: 8th International Conference on Web Information Systems Engineering (WISE 2007) 2007, 3-7 Dec 2007, Nancy, France.
- Lu, Jianguo; Yu, Yijun; Roy, Debashis and Saha, Deepa (2007). Web service composition: a reality check. In: The 8th International Conference on Web Information Systems Engineering (WISE'07), 03-07 Dec 2007, Nancy, France.
- Niu, Nan; Easterbrook, Steve and Yu, Yijun (2007). A taxonomy of asymmetric requirements aspects. In: 6th International Conference on Aspect-Oriented Software Development (AOSD'07) , 12-16 Mar 2007, Vancouver, Canada.
- Oliveira, Cristóvão and Wermelinger, Michel (2007). The CommUnity Workbench. Science of Computer Programming, 69(1-3) pp. 46–55.
- Olsen, Anneli; Rogers, Yvonne and Sharp, Helen (2007). The snap method. In: Beyond Current User Research: Designing Methods for New Users, Technologies, and Design Processes, 27 April 2007, San Jose, California, USA.
2006
- Bandara, Arosha K.; Kakas, Antonis; Lupu, Emil C. and Russo, Alessandra (2006). Using Argumentation Logic for Firewall Policy Specification and Analysis. In: Lecture Notes in Computer Science, 4269 pp. 185–196.
- Jackson, Michael (2006). What can we expect from program verification? IEEE Computer, 39(10) pp. 65–71.
- Lapouchnian, Alexei; Yu, Yijun; Liaskos, Sotirios and Mylopoulos, John (2006). Requirements-driven design of autonomic application software. In: 16th IBM Centre for Advanced Studies Conference, 16-19 Oct 2006, Toronto, Canada.
- Chantree, Francis; Nuseibeh, Bashar; De Roeck, Anne and Willis, Alistair (2006). Identifying nocuous ambiguities in natural language requirements. In: 14th IEEE International Requirements Engineering Conference (RE'06), IEEE, pp. 56–65.
- Haley, Charles B.; Laney, Robin; Moffett, Jonathan D. and Nuseibeh, Bashar (2006). Arguing satisfaction of security requirements. In: Mouratidis, Haralambos and Giorgini, Paolo eds. Integrating security and software engineering: advances and future vision. Hershey, PA and London: Idea Group Publishing, pp. 15–42.
- Petre, Marian (2006). Cognitive dimensions 'beyond the notation'. Journal of Visual Languages & Computing, 17(4) pp. 292–301.
- Sharp, Helen; Robinson, Hugh; Segal, Judith and Furniss, Dominic (2006). The Role of Story Cards and the Wall in XP teams: a distributed cognition perspective. In: AGILE Conference, 2006, IEEE, pp. 65–75.
- Chamberlain, Stephanie; Sharp, Helen and Maiden, Neil (2006). Towards a framework for integrating agile development and user-centred design. In: Abrahamsson, Pekka; Marchesi, Michele and Succi, Giancarlo eds. Extreme Programming and Agile Processes in Software Engineering: 7th International Conference, XP 2006, Oulu, Finland, June 17-22, 2006. Proceedings. Springer Berlin, pp. 143–153.
- Haley, Charles B.; Moffett, Jonathan D.; Laney, Robin and Nuseibeh, Bashar (2006). A framework for security requirements engineering. In: Software Engineering for Secure Systems Workshop (SESS'06), co-located with the 28th International Conference on Software Engineering (ICSE'06), 20-21 May 2006, Shanghai, China.
- Minocha, Shailey; Petre, Marian; Tzanidou, Ekaterini; van Dijk, Geke; Roberts, Dave; Gassman, Nick; Millard, Nicola; Day, Barry and Travis, David (2006). Evaluating e-commerce environments: approaches to cross-disciplinary investigation. In: CHI 06 extended abstracts on Human factors in computing systems - CHI 06 CHI 06, p. 1121.
- Charalambides, M.; Flegkas, P.; Pavlou, G.; Rubio-Loyola, J.; Bandara, A. K.; Lupu, E. C.; Russo, A.; Sloman, M. and Dulay, N. (2006). Dynamic policy analysis and conflict resolution for DiffServ quality of service management. In: 10th IEEE/IFIP Network Operations and Management Symposium (NOMS 2006), 3-7 April 2006, Vancouver, Canada, pp. 294–304.
- Bandara, Arosha K.; Lupu, Emil C.; Russo, Alessandra; Dulay, Naranker; Sloman, Morris; Flegkas, Paris; Charalambides, Marinos and Pavlou, George (2006). Policy refinement for IP differentiated services quality of service management. IEEE Transactions on Network and Service Management, 3(2) pp. 2–13.
- Haley, Charles B.; Laney, Robin C.; Moffett, Jonathan D. and Nuseibeh, Bashar (2006). Using trust assumptions with security requirements. Requirements Engineering, 11(2) pp. 138–151.
- Petre, Marian; Minocha, Shailey and Roberts, Dave (2006). Usability beyond the website: an empirically-grounded e-commerce evaluation instrument for the total customer experience. Behaviour & Information Technology, 25(2) pp. 189–203.
- Sharp, Helen; Petre, Marian and Johnson, Jeffrey (2006). Complexity through combination: an account of knitwear design. Design Studies, 27(2) pp. 183–222.
- Buckingham Shum, Simon; Selvin, A.M.; Sierhuis, Maarten; Conklin, Jeffrey; Haley, C.B. and Nuseibeh, Bashar (2006). Hypermedia support for argumentation-based rationale: 15 years on from gIBIS and QOC. In: Dutoit, A.; McCall, R.; Mistrik, I. and Paech, B. eds. Rationale Management in Software Engineering. Berlin: Springer-Verlag, pp. 111–132.
- Ernst, Neil A.; Yu, Yijun and Mylopoulos, John (2006). Visualizing non-functional requirements. In: First International Workshop on Requirements Engineering Visualisation (REV'06), 11-15 Sep 2006, Minneapolis, Minnesota, USA.
- Heath, Thomas; Motta, Enrico and Petre, Marian (2006). Person to person trust factors in word of mouth recommendation. In: Conference on Human Factors in Computing Systems (CHI'06), 22-27 Apr 2006, Montreal, Quebec, Canada.
- Liaskos, Sotirios; Lapouchnian, Alexei; Yu, Yijun; Yu, Eric and Mylopoulos, John (2006). On Goal-based Variability Acquisition and Analysis. In: 14th IEEE International Requirements Engineering Conference (RE'06), 11-15 Sep 2006, Mineapolis/St. Paul, USA.
- Mahfouz, Ayman; Barroca, Leonor; Laney, Robin and Nuseibeh, Bashar (2006). Patterns for service-oriented information exchange requirements. In: PLoP Pattern Languages of Programs 2006, 21-23 October 2006, Portland, Oregon.
- Quinn, Brendan; Barroca, Leonor; Nuseibeh, Bashar; Fernandez-Ramil, Juan; Rapanotti, Lucia; Thomas, Pete and Wermelinger, Michel (2006). Learning software engineering at a distance. IEEE Software, 23(6) pp. 36–43.
- Sharp, Helen and Robinson, Hugh (2006). A distributed cognition account of mature XP teams. In: Abrahamsson, P.; Marchesi, M. and Succi, G. eds. Extreme Programming and Agile Processes in Software Engineering. Lecture Notes in Computer Science, 4044/2006. Berlin, Germany: Springer, pp. 1–10.
- Tun, Thein and Hall, Jon G. (2006). Developer requirements in the PF approach. In: ed. Proceedings of the 2006 international workshop on Advances and applications of problem frames. New York: ACM Press, pp. 87–90.
- Tzanidou, E.; Minocha, S.; Petre, M. and Grayson, A. (2006). Revisiting web design guidelines by exploring users' expectations, preferences and visual search behaviour. In: McEwan, T.; Gulliksen, J. and Benyon, D. eds. People and Computers XIX — The Bigger Picture. London, UK: Springer, pp. 421–438.
2005
- Lu, Jianguo; Yu, Yijun and Mylopoulos, J. (2005). A lightweight approach to semantic web service synthesis. In: International Workshop on Challenges in Web Information Retrieval and Integration (WIRI'05), 8-9 April 2005, Tokyo, Japan.
- Oliveira, Cristóvão; Wermelinger, Michel; Fiadeiro, José Luiz and Lopes, Antónia (2005). Modelling the GSM handover protocol in CommUnity. Electronic Notes in Theoretical Computer Science, 141(3) pp. 3–25.
- Haley, Debra; Nuseibeh, Bashar; Thomas, Pete; Taylor, Josie and Lefrere, Paul (2005). The Learning Grid and E-Assessment using Latent Semantic Analysis. In: Ritrovato, P.; Allison, C.; Cerri, S.; Dimitrakos, T.; Gaeta, M. and Salerno, S. eds. Towards the Learning Grid. Advances in Human Learning Services. Frontiers in Artificial Intelligence and Applications, Volume. Amsterdam, Holland: IOS Press.
- Yu, Yijun; Dayani-Fard, Homayoun; Mylopoulos, John and Andritsos, Periklis (2005). Reducing Build Time through Precompilations for Evolving Large Software. In: 21st IEEE International Conference on Software Maintenance, 26-29 Sep 2005, Budapest, Hungary.
- Petre, Marian; Tzanidou, Ekaterini; Minocha, Shailey and Grayson, Andrew (2005). Combining Eye Tracking and Conventional Techniques for Indications of User-Adaptability. In: Human-Computer Interaction - INTERACT 2005, Lecture Notes in Computer Science, Springer, Berlin, pp. 753–766.
- Yu, Yijun; Wang, Yiqiao; Mylopoulos, J.; Liaskos, S.; Lapouchnian, A. and do Prado Leite, J.C.S. (2005). Reverse Engineering Goal Models from Legacy Code. In: 13th IEEE International Conference on Requirements Engineering (RE'05), 29 Aug - 2 Sep 2005, Paris, France.
- Crook, R.; Ince, D. and Nuseibeh, Bashar (2005). On Modelling access policies: relating roles to their organisational Context. In: Proceedings of 13th IEEE International Conference on Requirements Engineering, 29 Aug-2 Sept 2005, Paris, France.
- Hall, J.G.; Mistrik, I.; Nuseibeh, B. and Silva, A. (2005). Editorial: Relating software requirements and architectures. IEE Proceedings: Software, 152(4) pp. 141–142.
- Robinson, Hugh and Sharp, Helen (2005). Organisational culture and XP: three case studies. In: Proceedings of the Agile Conference 2005, 24-29 July 2005, Denver, Colorado, USA.
- Price, Blaine A.; Adam, Karim and Nuseibeh, Bashar (2005). Keeping ubiquitous computing to yourself: a practical model for user control of privacy. International Journal of Human-Computer Studies, 63(1-2) pp. 228–253.
- Sharp, Helen; Woodman, Mark and Hovenden, Fiona (2005). Using metaphor to analyse qualitative data: Vulcans and Humans in software development. Empirical Software Engineering, 10(3) 343 -365.
- Bandara, Arosha K.; Lupu, Emil C.; Russo, Alessandra; Dulay, Naranker; Sloman, Morris; Flegkas, Paris; Charalambides, Marinos and Pavlou, George (2005). Policy refinement for DiffServ quality of service. In: IEEE eTransactions on Network and Service Management, 3(2).
- Yu, Yijun; Lu, Jianguo; Mylopoulos, John; Sun, Weiwei; Xue, Jing-Hao and D'Hollander, Erik H. (2005). Making XML Document Markups International. Software: Practice and Experience, 35(1) pp. 1–14.
- Charalambides, M.; Flegkas, P.; Pavlou, G.; Bandara, A. K.; Lupu, E. C.; Russo, A.; Dulav, N.; Sloman, M. and Rubio-Loyola, J. (2005). Policy conflict analysis for quality of service management. In: Sixth IEEE International Workshop on Policies for Distributed Systems and Networks, 6-8 June 2005, Stockholm, Sweden, pp. 99–108.
- Dayani-Fard, Homayoun; Yu, Yijun; Mylopoulos, John and Periklis, Andritsos (2005). Improving the build architecture of legacy C/C++ software systems. In: 8th International Conference on Fundamental Approaches to Software Engineering (FASE), 04-08 Apr 2005, Edinburgh, UK.
- do Prado Leite, Julio Cesar Sampaio; Yu, Yijun; Liu, Lin; Yu, Eric S.K. and Mylopoulos, John (2005). Quality-Based Software Reuse. In: 17th International Conference on Advanced Information Systems Engineering (CAiSE'05), 13-17 Jun 2005, Porto, Portugal.
- Haley, Charles B.; Moffett, Jonathan D.; Laney, Robin and Nuseibeh, Bashar (2005). Arguing security: validating security requirements using structured argumentation. In: Third Symposium on Requirements Engineering for Information Security (SREIS'05) held in conjunction with the 13th International Requirements Engineering Conference (RE'05), 29 Aug 2005, Paris, France.
- Jackson, Michael (2005). Problem structure and dependable architecture. In: De Lemos, Rojerio; Gacek, Cristina and Romanovsky, Alexander B. eds. Architecting Dependable Systems III. Lecture Notes in Computer Science (3549). Berlin: Springer, pp. 322–330.
- Lapouchnian, Alexei; Liaskos, Sotoris; Mylopoulos, John and Yu, Yijun (2005). Towards requirements-driven autonomic systems design. In: DEAS 2005 Design and Evolution of Autonomic Application Software, 21 May 2005, St. Louis, Missouri, USA.
- Liaskos, Sotirios; Lapouchnian, Alexei; Wang, Yiqiao; Yu, Yijun and Easterbrook, Steve (2005). Configuring common personal software: a requirements-driven approach. In: 13th IEEE International Conference on Requirements Engineering, 29 Aug - 2 Sep 2005, Paris, France.
- Mens, Tom; Wermelinger, Michel; Ducasse, Stéphane; Demeyer, Serge; Hirschfeld, Robert and Jazayeri, Mehdi (2005). Challenges in Software Evolution. In: 8th International Workshop on Principles of Software Evolution, 5-6 September 2005, Lisbon, Portugal.
- Robinson, Hugh and Sharp, Helen (2005). The social side of technical practices. In: Baumeister, Hubert; Marchesi, Michele and Holcombe, Mike eds. Extreme Programming and Agile Processes in Software Engineering: Proceedings of the 6th International Conference, XP 2005, Sheffield, UK, June 18-23, 2005. Lecture Notes in Computer Science, 3556 (3556). Berlin, Germany: Springer, pp. 100–108.
- Rosewell, Jonathan; Johnson, Jeffrey; Hirst, Tony and Price, Blaine (2005). Robotics and the meaning of life: a practical guide to things that think. In: CAL '05 'Virtual Learning?', 4-6 April 2005, Bristol, UK.
- Segal, Judith; Grinyer, Antony and Sharp, Helen (2005). The type of evidence produced by empirical software engineers. In: ed. Proceedings of the 2005 workshop on Realising evidence-based software engineering. New York, NY, USA: ACM Press, pp. 1–4.
- Sharp, Helen and Robinson, Hugh (2005). Some social factors of software engineering: the maverick, community and technical practices. In: ACM SIGSOFT Software Engineering Notes, 30(4).
- Tzanidou, Ekaterini; Petre, Marian; Minocha, Shailey and Grayson, Andrew (2005). Combining eye tracking and conventional techniques for indications of user-adaptability. Lecture Notes in Computer Science, 3585 pp. 753–766.
- Wermelinger, Michel and Dias, Artur Miguel (2005). A Prolog toolkit for formal languages and automata. In: Proceedings of the 10th annual SIGCSE Conference on Innovation and Technology in Computer Science Education, 27-29 June 2005, Caparica, Portugal, ACM.
- Zhang, Charles; Jacobsen, Hans-Arno and Yu, Yijun (2005). Linking goals to aspects. In: Early Aspects 2005: Aspect-Oriented Requirements Engineering and Architecture Design, 15 March 2005, Chicago, Illinois, USA.
- Zhang, Qing; Chen, Huiqiong; Yu, Yijun; Xie, Zhipeng and Shi, Baile (2005). Dynamically self-organized service composition in wireless ad hoc networks. In: 5th VLDB Workshop on Technologies for E-Services , 29 August - 3 September 2004, Toronto, Canada.
2004
- Jackson, Michael (2004). Routing optimizations for telecomms network system and method. Michael Jackson, 6829346.
- Sharp, Helen and Robinson, Hugh (2004). An Ethnographic study of XP practice. Empirical Software Engineering, 9(4) pp. 353–375.
- Wermelinger, Michel; Koutsoukos, Georgios; Lourenço, Hugo; Avillez, Richard; Gouveia, João; Andrade, Luís and Fiadeiro, José Luiz (2004). Enhancing dependability through flexible adaptation to changing requirements. In: de Lemos, Rogério; Gacek, Cristina and Romanovsky, Alexander eds. Architecting Dependable Systems II. Lecture Notes in Computer Science (3069). Springer-Verlag, pp. 3–24.
- Rapanotti, L.; Hall, J.G.; Jackson, M. and Nuseibeh, B. (2004). Architecture-driven problem decomposition. In: 12th IEEE International Conference on Requirements Engineering (RE 2004), 6-11 Sep 2004, Kyoto, Japan.
- Haley, Charles B.; Laney, Robin C.; Moffett, Jonathan D. and Nuseibeh, Bashar (2004). The Effect of trust assumptions on the elaboration of security requirements. In: 12th IEEE International Requirements Engineering Conference (RE'04), 6-10 Sep 2004, Kyoto, Japan.
- Yu, Yijun; Leite, J.C.S.P. and Mylopoulos, J. (2004). From Goals to Aspects: Discovering Aspects from Requirements Goal Models. In: 12th IEEE International Requirements Engineering Conference, 6-10 Sep 2004, Kyoto, Japan.
- Laney, Robin; Barroca, Leonor; Jackson, Michael and Nuseibeh, Bashar (2004). Composing requirements using problem frames. In: Proceedings of the 12th IEEE International Requirements Engineering Conference (RE 2004), IEEE, pp. 122–131.
- Petre, Marian (2004). How expert engineering teams use disciplines of innovation. Design Studies, 25(5) pp. 477–493.
- Petre, Marian (2004). Team coordination through externalised mental imagery. International Journal of Human-Computer Studies, 61(2) pp. 205–218.
- Petre, Marian (2004). Team coordination through externalized mental imagery. International Journal of Human-Computer Studies, 61(2) pp. 205–218.
- Sharp, Helen; Woodman, Mark and Hovenden, Fiona (2004). Tensions around the adoption and evolution of software quality management systems: a discourse analytic approach. International Journal of Human-Computer Studies, 61(2) pp. 219–236.
- Bandara, Arosha; Lupu, Emil C; Moffett, Jonathan and Russo, Alessandra (2004). A Goal-based Approach to Policy Refinement. In: 5th IEEE International Workshop on Policies for Distributed Systems and Networks, 7-9 Jun 2004, Yorktown Heights, USA.
- Haley, Charles B.; Laney, Robin C. and Nuseibeh, Bashar (2004). Using Problem Frames and projections to analyze requirements for distributed systems. In: Proceedings of the Tenth International Workshop on Requirements Engineering: Foundation for Software Quality (REFSQ'04), co-located with the 16th International Conference on Advanced Information Systems Engineering (CAiSE'04), 7-8 Jun 2004, Riga, Latvia.
- Petre, Marian and Price, Blaine (2004). Using robotics to motivate 'back door' learning. Education and Information Technologies, 9(2) pp. 147–158.
- Minocha, Shailey and Sharp, Helen (2004). Learner-Centred Design and Evaluation of Web-Based E-Learning Environments. In: The 7th HCI Educators Workshop: Effective Teaching and Training in HCI, 1-2 April 2004, University of Central Lancashire, Preston.
- Haley, Charles B.; Laney, Robin C.; Moffett, Jonathan D. and Nuseibeh, Bashar (2004). Picking battles: The impact of trust assumptions on the elaboration of security requirements. In: Proceedings of the Second International Conference on Trust Management (iTrust'04), 29 Mar - 1 Apr 2004, Oxford, UK.
- Haley, Charles B.; Laney, Robin C. and Nuseibeh, Bashar (2004). Deriving security requirements from crosscutting threat descriptions. In: Proceedings of the 3rd international conference on aspect-oriented software development, ACM Press, New York, USA, pp. 112–121.
- Barroca, Leonor; Fiadeiro, J.L.; Jackson, M.; Laney, Robin and Nuseibeh, B. (2004). Problem frames: a case for coordination. In: De Nicola, Rocco; Ferrari, Gianluigi and Meredith, Greg eds. Coordination models and languages: 6th International Conference, COORDINATION 2004 Pisa Italy, February 24-27, 2004: Proceedings. Lecture notes in computer science, 2949 (2949/2004). Heidleburg, Germany: Springer, pp. 5–19.
- Wermelinger, Michel and Margaria-Steffen, Tiziana eds. (2004). Fundamental Approaches to Software Engineering: 7th International Conference Proceedings. Lecture Notes in Computer Science, 2984. Berlin: Springer-Verlag.
- Bradbury, Jeremy S.; Cordy, James R.; Dingel, Juergen and Wermelinger, Michel (2004). A survey of self-management in dynamic software architecture specifications. In: Proceedings of the 1st ACM SIGSOFT Workshop on Self-managed Systems, 31 Oct - 1 Nov 2004, ACM, pp. 28–33.
- Haley, Debra; Nuseibeh, Bashar; Sharp, Helen and Taylor, Josie (2004). The conundrum of categorising requirements: managing requirements for learning on the move. In: 12th International Requirements Engineering Conference (RE'04), 6-10 Sept 2004, Kyoto, Japan.
- Johnson, Jeffrey and Price, Blaine A. (2004). Complexity science and representation in robot soccer. In: Polani, Daniel; Browning, Brett; Bonarini, Andrea and Yoshida, Kazuo eds. RoboCup 2003: Robot Soccer World Cup VII. Lecture Notes in Computer Science, 3020. Berlin: Springer, pp. 67–76.
- Lin, Luncheng; Nuseibeh, Bashar; Ince, Darrel and Jackson, Michael (2004). Using abuse frames to bound the scope of security problems. In: ed. 12th IEEE International Requirements Engineering Conference (RE'04). IEEE Computer Society, pp. 354–355.
- Robinson, Hugh; Segal, Judith and Sharp, Helen (2004). The case for empirical studies of the practice of software development. In: Jedlitschka, Andreas and Ciolkowski, Marcus eds. The Future of Empirical Studies in Software Engineering. Workshop Series on Empirical Software Engineering, 2. Stuttgart, Germany: Fraunhofer IRB Verlag, pp. 98–107.
- Robinson, Hugh and Sharp, Helen (2004). The characteristics of XP teams. In: Eckstein, Jutta and Baumeister, Hubert eds. Extreme Programming and Agile Processes in Software Engineering. Lecture Notes in Computer Science (3092). Berlin, Germany: Springer, pp. 135–147.
- Yu, Y.; Beyls, K. and D'Hollander, E. (2004). Performance visualization using XML representations. In: 8th International Conference on Information Visualisation, 14-16 July 2004, London, UK.
- Yu, Yijun; Beyls, Kristof and D'Hollander, Erik H. (2004). Visualizing the Impact of the Cache on Program Execution. Journal for the Integrated Study of AI, Cognitive Science and Applied Epistemology, 19(3-4) pp. 1–23.
- Yu, Yijun and D'Hollander, E. H. (2004). Non-uniform dependences partitioned by recurrence chains. In: 2004 International Conference on Parallel Processing (ICPP'04), 15-18 Aug 2004, Montreal, Canada.
2003
- Hayes, Ian J.; Jackson, Michael A. and Jones, Cliff B. (2003). Determining the specification of a control system from that of its environment. In: FME 2003: Formal Methods: International Symposium of Formal Methods Europe Pisa, Italy, September 8-14, 2003, Lecture Notes in Computer Science, Springer Berlin, Heidelberg, Germany, pp. 154–169.
- Crook, Robert; Ince, Darrel and Nuseibeh, Bashar (2003). Modelling access policies using roles in requirements engineering. Information and Software Technology, 45(14) pp. 979–991.
- Bandara, Arosha; Lupu, Emil C and Russo, Alessandra (2003). Using Event Calculus to Formalise Policy Specification and Analysis. In: IEEE 4th International Workshop on Policies for Distributed Systems and Networks, 4-6 Jun 2003, Lake Como, Italy.
- Sun, Weiwei; Shi, Weibin; Shi, Bole and Yu, Yijun (2003). A cost-efficient scheduling algorithm of on-demand broadcasts. Wireless Networks, 9(3) pp. 239–247.
- Haley, Charles and Nuseibeh, Bashar (2003). Going on-line on a shoestring: An experiment in concurrent development of requirements and architecture. In: International Conference on Advances in Infrastructure for Electronic Business, Education, Science, Medicine, and Mobile Technologies on the Internet, 6-12 Jan 2003, L'Aquila Italy.
- Lopes, Antónia; Wermelinger, Michel and Fiadeiro, José Luiz (2003). Higher-order architectural connectors. ACM Transactions on Software Engineering and Methodology, 12(1) pp. 64–104.
- Fiadeiro, José Luiz; Lopes, Antónia and Wermelinger, Michel (2003). A mathematical semantics for architectural connectors. In: Backhouse, R and Gibbons, J eds. Generic programming: advanced lectures. Lecture notes in computer science (2793). Berlin, Germany: Springer-Verlag, pp. 178–221.
- Johnson, Jeffrey and Price, Blaine (2003). Representing Patterns of autonomous agent dynamics in multi-robot systems. In: International Journal of Human-Computer Studies, 63(1-2) pp. 228–253.
- Lin, Luncheng; Nuseibeh, Bashar; Ince, Darrel; Jackson, Michael and Moffett, Jonathan (2003). Introducing abuse frames to analyse security requirements. In: Proceedings of the 11th International Conference on Requirements Engineering, 8th-12th Sept 2003, Monterey, USA.
- Price, Blaine A.; Richards, Mike; Petre, Marian; Hirst, Anthony and Johnson, Jeffrey (2003). Developing Robotics e-teaching for teamwork. International Journal of Continuing Engineering Education and Life-long Learning, 13(1-2) pp. 190–205.
- Robinson, Hugh and Sharp, Helen (2003). XP culture: why the twelve practices both are and are not the most significant thing. In: ed. Proceedings of the Conference on Agile Development. IEEE, p. 12.
- Sharp, Helen; Taylor, Josie; Löber, Andreas; Frohberg, Dirk; Mwanza, Daisy and Murelli, Elena (2003). Establishing user requirements for a mobile learning environment. In: Conference proceedings of Eurescom 2003, 29 Sept- 1 Oct 2003, Heidelberg, Germany.
- Yu, Y; Mylopoulos, J; Leite, J.C.S.P; Liu, L and D'Hollander, E.H (2003). Software refactoring guided by multiple soft-goals. In: 1st workshop on Refactoring: Achievements, Challenges, and Effects (REFACE'03), 13-16 November 2003, Victoria, Canada.
2002
- Beyls, Kristof; D'Hollander, Erik H. and Yu, Yijun (2002). Visualization enables the programmer to reduce cache misses. In: IASTED International Conference on Parallel and Distributed Computing and Systems (PDCS 2002), 4-6 November 2002, Cambridge, MA, USA.
- Thomas, Pete; Price, Blaine; Paine, Carina and Richards, Michael (2002). Remote electronic examinations: student experiences. British Journal of Educational Technology, 33(5) pp. 537–549.
- Hall, J.G.; Jackson, M.; Laney, R. C.; Nuseibeh, B. and Rapanotti, L. (2002). Relating software requirements and architectures using problem frames. In: Proceedings of the IEEE Joint International Conference on Requirements Engineering, 2002, 09-13 Sep 2002, Essen, Germany.
- Wermelinger, Michel and Fiadeiro, José Luiz (2002). A Graph Transformation Approach to Software Architecture Reconfiguration. Science of Computer Programming, 44(2) pp. 133–155.
- Russo, Alessandra; Miller, Rob; Nuseibeh, Bashar and Kramer, Jeff (2002). An abductive approach for analysing event-based requirements specifications. In: 18th International Conference on Logic Programming, 29 July - 01 August 2002, Copenhagen, Denmark.
- Petre, Marian (2002). Mental imagery, visualisation tools and team work. In: Proceedings of the Second Program Visualisation Workshop pp. 3–14.
- Gervasi, Vincenzo and Nuseibeh, Bashar (2002). Lightweight Validation of Natural Language Requirements. Software: Practice and Experience, 32(2) pp. 113–133.
- Preece, Jenny; Rogers, Yvonne and Sharp, Helen eds. (2002). Interaction Design: Beyond Human-Computer Interaction. John Wiley.
- Crook, Robert; Ince, Darrel; Lin, Luncheng and Nuseibeh, Bashar (2002). Security Requirements Engineering: when anti-requirements hit the fan. In: Proc IEEE International Conference on Requirements Engineering, 8-13 Sept 2002, Germany.
- Lopes, Antónia; Fiadeiro, José Luiz and Wermelinger, Michel (2002). Architectural primitives for distribution and mobility. In: Proceedings of the 10th ACM SIGSOFT symposium on Foundations of software engineering, ACM Press, pp. 41–50.
- Mens, Kim; Mens, Tom and Wermelinger, Michel (2002). Maintaining software through intentional source-code views. In: Proceedings of the 14th international conference on Software engineering and knowledge engineering, ACM International Conference Proceeding Series, pp. 289–296.
2001
- Jackson, Michael (2001). Problem Frames: Analysing and Structuring Software Development Problems. New York: Addison-Wesley.
- Yu, Yijun and D'Hollander, Erik H. (2001). Loop Parallelization using the 3D Iteration Space Visualizer. Journal of Visual Languages & Computing, 12(2) pp. 163–181.
- Nuseibeh, B. (2001). Weaving together requirements and architecture. Computer, 34(3) pp. 115–119.
- Demeyer, Serge; Mens, Tom and Wermelinger, Michel (2001). Towards a software evolution benchmark. In: IWPSE '01 Proceedings of the 4th International Workshop on Principles of Software Evolution, ACM, pp. 174–177.
- Wermelinger, Michel; Lopes, Antónia and Fiadeiro, José Luiz (2001). A Graph based architectural (re)configuration language. In: Proceedings of the 8th European Software Engineering Conference held jointly with 9th ACM SIGSOFT International Symposium on Foundations of Software Engineering, ACM, pp. 21–32.
1999
- Wermelinger, Michel (1999). Specification of Software Architecture Reconfiguration. PhD thesis Universidade Nova de Lisboa.
1998
- Wermelinger, Michel (1998). Towards a chemical model for software architecture reconfiguration. IEE Proceedings - Software, 145(5) pp. 130–136.
- Wermelinger, Michel and Fiadeiro, José Luiz (1998). Connectors for mobile programs. IEEE Transactions on Software Engineering, 24(5) pp. 331–341.
- Stasko, John; Domingue, John; Brown, Marc H and Price, Blaine eds. (1998). Software Visualization: Programming as a Multimedia Experience. Cambridge, Mass: MIT Press.
1997
- Price, Blaine and Petre, Marian (1997). Teaching programming through paperless assignments: an empirical evaluation of instructor feedback. In: Proceedings of the 2nd conference on Integrating technology into computer science education, ACM, New York, NY, pp. 94–99.
- Wermelinger, Michel (1997). A different perspective on canonicity. In: Conceptual Structures: Fulfilling Peirce's Dream: Fifth International Conference on Conceptual Structures, ICCS'97 Seattle, Washington, USA, August 3–8, 1997 Proceedings, Lecture Notes in Computer Science (Lecture Notes in Computer Science), Springer, pp. 110–124.
- Wermelinger, Michel (1997). A hierarchic architecture model for dynamic reconfiguration. In: Software Engineering for Parallel and Distributed Systems, 1997. Proceedings., Second International Workshop on , IEEE, pp. 243–254.
- Wermelinger, Michel (1995). Teoria Básica das Estruturas Conceptuais. MPhil thesis Universidade Nova de Lisboa.
1995
- Wermelinger, Michel (1995). Conceptual graphs and first-order logic. In: Conceptual Structures: Applications, Implementation and Theory: Third International Conference on Conceptual Structures, ICCS '95 Santa Cruz, CA, USA, August 14–18, 1995 Proceedings, Lecture Notes in Computer Science (Lecture Notes in Artificial Intelligence), Springer, pp. 323–337.
1994
- Jones, Ann and Petre, Marian (1994). Computer-based practical work at a distance: a case study. Computers and Education, 22(1-2) pp. 27–37.
- Wermelinger, Michel and Lopes, José Gabriel (1994). Basic conceptual structures theory. In: Conceptual Structures: Current Practices, Lecture Notes in Computer Science, Springer, pp. 144–159.
1993
- Wermelinger, Michel and Bejan, Alex (1993). Conceptual structures for modeling in CIM. In: Conceptual Graphs for Knowledge Representation: First International Conference on Conceptual Structures, ICCS'93 Quebec City, Canada, August 4–7, 1993 Proceedings, Lecture Notes in Computer Science (Lecture Notes in Artificial Intelligence), Springer, pp. 345–360.
1992
- Wermelinger, Michel and Lopes, José Gabriel (1993). An X-Windows Toolkit for knowledge acquisition and representation based on conceptual structures. In: Conceptual Structures: Theory and Implementation: 7th Annual Workshop Las Cruces, NM, USA, July 8–10, 1992 Proceedings, Lecture Notes in Computer Science (Lecture Notes in Artificial Intelligence), Springer, pp. 262–271.
1991
- Petre, Marian (1991). Shifts in reasoning about software and hardware systems: do operational models underpin declarative ones? In: Psychology of Programming Interest Group , 3-5 January 1991, Hatfield.
Automated Software Engineering
- art - automated refactoring tool
- blinkit - invariant traceability
- intt - identifier name tokenizer tool
Requirements Engineering
- miki -- Modeling wiki openargue -- argumentation
- openpf -- problem frames tool support
- openome -- i*/OME tool support
- pfcontext
- risa
Software Adaptation & Evolution
Empirical Studies of Software Development
Introduction to Cyber Security (MOOC)
Collaborative Security
Ariadne: Topology Aware Adaptive Security for Cyber-Physical Systems
Cedar - Engineering Adaptive User Interfaces for Enterprise Applications
Contravision - Contrasting Visions of Future Technology